Role of security in manufacturing: protect assets now
Role of security in manufacturing: protect assets now

Manufacturing security often gets dismissed as a basic checkbox until a breach exposes millions in losses. Yet integrated security strategies protect not only physical assets but also intellectual property, operational continuity, and regulatory standing. This guide unpacks the critical role security plays across manufacturing environments, from cybersecurity defenses against ransomware to compliance frameworks that prevent costly penalties. You'll discover actionable measures to strengthen your facility's protection and align technology with policy for resilient operations.
Table of Contents
- Key takeaways
- Understanding the multifaceted role of security in manufacturing
- Core cybersecurity measures essential for manufacturing environments
- Compliance and regulatory frameworks impacting manufacturing security
- Integrating technology and policy for a resilient manufacturing security strategy
- Enhance your manufacturing security with expert solutions
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Integrated security approach | Security blends physical protection and cybersecurity to safeguard assets, operations, and regulatory standing. |
| Network segmentation | Isolating production from corporate networks limits breach spread and protects critical control systems. |
| Regular vulnerability assessments | Ongoing assessments and penetration tests reveal weaknesses before attackers exploit them. |
| Cross domain collaboration | Coordinated reviews between physical security and IT teams identify gaps that single domain approaches miss. |
Understanding the multifaceted role of security in manufacturing
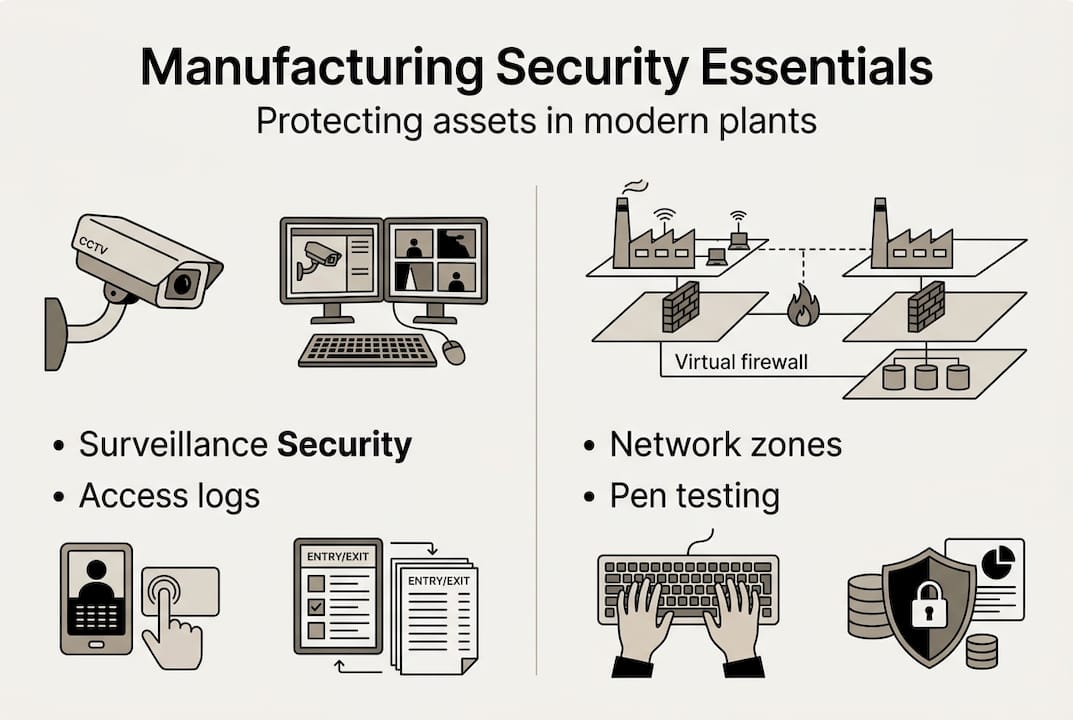
Manufacturing security extends far beyond locked doors and surveillance cameras. You're protecting physical infrastructure, controlling site access, and defending industrial control systems against sophisticated cyber threats. Security consulting for integrators addresses these overlapping challenges by recognizing that production floors now operate as interconnected digital ecosystems vulnerable to ransomware, espionage, and supply chain attacks.
Cyber threats targeting manufacturing have evolved dramatically. Ransomware groups specifically hunt industrial targets because production downtime creates immediate financial pressure. Espionage campaigns steal proprietary designs and processes, undermining competitive advantages. Supply chain vulnerabilities allow attackers to infiltrate through trusted vendor connections, bypassing perimeter defenses entirely.
Physical security remains equally critical. Surveillance systems monitor entry points and restricted zones. Personnel screening prevents insider threats by vetting employees and contractors before granting facility access. Access control systems limit who can reach sensitive areas like server rooms or production lines handling classified projects.
The convergence of operational technology and information technology creates unique challenges. Legacy equipment often lacks modern security features, running outdated software that can't be easily patched. OT systems prioritize uptime over security updates, creating persistent vulnerabilities. When these systems connect to corporate IT networks for data analytics or remote monitoring, they expose critical infrastructure to threats designed for standard enterprise environments.
Pro Tip: Schedule quarterly reviews where physical security teams and IT professionals jointly assess how access controls, network segmentation, and monitoring systems work together, identifying gaps that single-domain approaches miss.
Effective manufacturing security requires coordinated strategies addressing both domains simultaneously. Physical breaches can enable cyber attacks when intruders access network equipment. Conversely, cyber compromises can disable physical security systems or unlock doors remotely. Your security posture strengthens dramatically when protocols integrate these traditionally separate functions into unified protection frameworks.
Core cybersecurity measures essential for manufacturing environments
Network segmentation stands as your first line of defense against lateral movement during attacks. By isolating production networks from corporate systems, you contain breaches and prevent attackers from pivoting between environments. Critical control systems operate on separate network segments with strict firewall rules governing inter-segment communication. This architecture limits blast radius when incidents occur.

Regular vulnerability assessments identify weaknesses before attackers exploit them. Penetration testing services simulate real-world attack scenarios, revealing security gaps in both IT and OT systems. These assessments uncover misconfigurations, unpatched software, weak authentication mechanisms, and exposed services that automated scanners might miss. Quarterly testing provides ongoing visibility into your evolving threat landscape.
Employee cybersecurity awareness directly impacts your risk profile. Social engineering attacks target manufacturing workers who may lack technical security training. Phishing campaigns impersonate vendors or executives to steal credentials or deploy malware. Spear phishing uses researched details about your operations to craft convincing messages. Training programs must address manufacturing-specific scenarios like fake maintenance requests or fraudulent shipping notifications.
Penetration testing goes beyond automated scans by employing human expertise to chain vulnerabilities and test incident response capabilities. Testers attempt to breach networks, escalate privileges, access sensitive data, and move laterally just as real adversaries would. This process validates whether your risk management strategies for IT security translate into practical defenses under pressure.
| Cybersecurity measure | Primary benefit | Implementation complexity |
|---|---|---|
| Network segmentation | Limits attack spread | Medium to high |
| Vulnerability scanning | Identifies known weaknesses | Low to medium |
| Penetration testing | Discovers exploitable gaps | High |
| Employee training | Reduces human error | Low to medium |
| Multi-factor authentication | Blocks credential theft | Medium |
Implementing these controls follows a logical sequence. First, conduct a comprehensive security assessment to understand your current posture and identify critical assets requiring protection. Second, prioritize vulnerabilities based on potential impact and exploitability, addressing high-risk items immediately. Third, deploy technical controls like segmentation and authentication while simultaneously launching employee training programs. Fourth, establish continuous monitoring to detect anomalies and potential breaches in real time. Fifth, schedule regular penetration tests and vulnerability assessments to validate control effectiveness and discover new weaknesses.
Pro Tip: Incorporate realistic manufacturing scenarios into security training, such as handling suspicious USB drives found near equipment or verifying unusual production schedule changes, to make lessons directly applicable to daily operations.
Multi-factor authentication adds critical protection for remote access and administrative accounts. Even when attackers steal passwords through phishing or credential stuffing, they can't authenticate without the second factor. Implement MFA for VPN connections, industrial control system interfaces, and any remote management tools accessing production environments.
Compliance and regulatory frameworks impacting manufacturing security
Regulatory frameworks establish baseline security requirements that manufacturing organizations must meet to operate legally and maintain customer trust. The NIST Cybersecurity Framework provides voluntary guidelines for managing cybersecurity risks through five core functions: identify, protect, detect, respond, and recover. ISA/IEC 62443 specifically addresses industrial automation and control system security, offering detailed technical requirements for securing OT environments. The Cybersecurity Maturity Model Certification applies to defense contractors, mandating specific security practices based on the sensitivity of controlled unclassified information handled.
Security compliance tips for 2026 emphasize that adherence extends beyond avoiding penalties. Compliance demonstrates due diligence to customers, insurers, and partners. It provides structured approaches to security that prevent ad-hoc implementations. Frameworks guide resource allocation by identifying which controls deliver maximum risk reduction.
| Framework | Primary scope | Focus areas | Applicability |
|---|---|---|---|
| NIST Cybersecurity Framework | Enterprise-wide | Risk management, incident response | All manufacturing sectors |
| ISA/IEC 62443 | Industrial control systems | OT security, network segmentation | Process manufacturing, discrete manufacturing |
| CMMC | Defense supply chain | Controlled unclassified information protection | Defense contractors and subcontractors |
| OSHA requirements | Workplace safety | Physical security, hazard communication | All US manufacturing facilities |
Maintaining ongoing compliance requires systematic approaches rather than one-time efforts. Regular internal audits verify that implemented controls remain effective and documented. Continuous monitoring tracks configuration changes, access patterns, and security events that might indicate control failures. Incident response plans must align with regulatory reporting requirements, ensuring you notify appropriate authorities within mandated timeframes. Documentation practices prove compliance during external audits by maintaining evidence of security activities, training completion, and remediation efforts.
Best practices for audit readiness include:
- Maintain centralized documentation of all security policies, procedures, and control implementations
- Conduct quarterly internal audits using the same standards external auditors will apply
- Implement automated compliance monitoring tools that continuously assess control effectiveness
- Establish clear ownership for each compliance requirement with designated responsible parties
- Create audit trails for all administrative actions, configuration changes, and security events
- Schedule regular training to keep security teams current on evolving regulatory requirements
Compliance frameworks evolve as threats change and technology advances. Staying current requires monitoring regulatory updates, participating in industry groups, and engaging with compliance experts who track changes across multiple standards. What satisfied auditors last year may fall short of new requirements, making continuous improvement essential rather than optional.
Integrating technology and policy for a resilient manufacturing security strategy
Technology integration enables real-time threat detection and automated response capabilities that human teams can't match in speed or consistency. Security information and event management systems aggregate logs from across your infrastructure, correlating events to identify attack patterns. Automated response playbooks execute predefined actions when specific threats appear, containing incidents before they escalate. Custom development and automation tailors these capabilities to your unique manufacturing workflows, ensuring security measures enhance rather than hinder production.
Policy frameworks must align precisely with technological capabilities to achieve effectiveness. Policies define acceptable use, access requirements, incident reporting procedures, and consequences for violations. When policies reference specific tools and processes your organization actually uses, employees understand exactly what's expected. Generic policies copied from templates often fail because they don't match operational reality, creating confusion and non-compliance.
Employee training and organizational culture determine whether even the best technology and policies succeed. Security awareness can't be a once-yearly checkbox exercise. Ongoing training keeps threats and procedures fresh in employees' minds. Simulated phishing campaigns test awareness and identify individuals needing additional support. Recognition programs reward employees who report suspicious activity, reinforcing vigilant behavior.
Combining tools and policies into cohesive security frameworks follows these steps:
- Conduct comprehensive assessments identifying current technology stack, existing policies, and security gaps across both domains
- Customize solutions to match your specific manufacturing processes, equipment types, and operational constraints rather than deploying generic templates
- Train employees on both the technical tools they'll use and the policy requirements they must follow, explaining why each matters
- Monitor continuously using automated systems supplemented by regular manual reviews to catch what automation misses
- Improve iteratively by analyzing incidents, near-misses, and audit findings to refine both technology configurations and policy language
Pro Tip: Partner with specialized security consultants who understand manufacturing environments to design automation solutions that account for production uptime requirements, legacy equipment constraints, and operational technology security challenges unique to industrial settings.
Effective integration recognizes that technology alone can't solve security challenges. Firewalls and intrusion detection systems fail when employees click phishing links or share passwords. Conversely, policies without enforcement mechanisms become ignored suggestions. The synergy between robust technical controls and clear, enforced policies creates defense in depth that addresses both technological and human vulnerabilities.
Continuous improvement cycles keep security strategies relevant as threats evolve and operations change. Security insights and industry news help you stay informed about emerging attack techniques, new compliance requirements, and innovative defense technologies. Regular strategy reviews assess whether current approaches still address your highest risks or need adjustment based on business changes, threat landscape shifts, or lessons from security incidents.
Enhance your manufacturing security with expert solutions
Implementing comprehensive security strategies requires specialized expertise that many manufacturing organizations lack internally. Stonos Solutions delivers tailored security assessments, vulnerability analyses, and risk management strategies specifically designed for industrial environments. Our penetration testing services simulate real-world attacks against your manufacturing systems, identifying exploitable weaknesses before adversaries find them.

Our custom development services create automated security solutions that integrate seamlessly with your existing manufacturing workflows, enhancing protection without disrupting production. From network segmentation design to compliance framework implementation, our certified experts bring deep experience across manufacturing, industrial, and enterprise environments. Explore our complete range of security services offerings to discover how we can strengthen your facility's defenses and ensure regulatory compliance.
Frequently asked questions
What are the biggest security risks in manufacturing?
Manufacturing faces ransomware attacks that encrypt production systems and demand payment for restoration, creating immediate operational and financial pressure. Physical security breaches allow unauthorized access to facilities, enabling theft of equipment, intellectual property, or sabotage of production lines. Insider threats from disgruntled employees or contractors with legitimate access pose significant risks because they bypass perimeter defenses. Supply chain vulnerabilities occur when trusted vendors or partners become compromise vectors, allowing attackers to infiltrate through established business relationships.
How does compliance impact manufacturing security?
Compliance frameworks establish mandatory security baselines that organizations must implement to operate legally and maintain contracts with customers requiring specific certifications. Meeting standards like NIST, ISA/IEC 62443, or CMMC protects against regulatory penalties, lawsuits, and loss of business relationships. Compliance also provides structured approaches to security that guide resource allocation and ensure consistent protection across operations. Regular audits verify control effectiveness and identify gaps before they become exploited vulnerabilities.
What role do employees play in manufacturing security?
Employees serve as the first line of defense by recognizing and reporting suspicious activities, phishing attempts, and physical security concerns before they escalate into breaches. Their adherence to security policies determines whether technical controls remain effective or get circumvented through workarounds and shortcuts. Training programs must address manufacturing-specific threats and scenarios to build relevant awareness. Creating a security-conscious culture where reporting concerns is encouraged and rewarded strengthens overall protection more than technology alone can achieve.
Recommended
Louis Romano
Need Security Consulting?
Our expert team is ready to help you enhance your security posture.
Contact Us Today Download Capability StatementRelated Articles
Enterprise Security Checklist for Healthcare Compliance Success
Explore an actionable enterprise security checklist tailored for healthcare organizations. Follow a step-by-step process to ensure HIPAA compliance and risk management.
Read More7 Key Types of Cybersecurity Assessments for Healthcare
Learn about 7 essential types of cybersecurity assessments for healthcare organizations and get actionable tips to boost compliance and security.
Read MoreRisk management strategy guide 2026: advanced tactics
Master advanced risk management strategies for healthcare, government, and industrial sectors. Build integrated compliance frameworks, reduce incidents, and enhance security posture in 2026.
Read More