Vulnerability Assessment: Ensuring HIPAA Compliance in Healthcare
Vulnerability Assessment: Ensuring HIPAA Compliance in Healthcare
Finding security gaps across patient databases and medical devices is a daily challenge for American healthcare organizations. Regulatory pressure from HIPAA makes identifying and managing vulnerabilities a legal requirement, not just a technical goal. By focusing on a systematic process that identifies, quantifies, and prioritizes security weaknesses, you transform scattered security concerns into detailed actions your team can tackle. This approach lays the foundation for protecting patient data and proving compliance during audits.
Table of Contents
- Defining Vulnerability Assessment In Cybersecurity
- Types Of Vulnerability Assessments For Healthcare
- How Vulnerability Assessment Processes Work
- HIPAA Compliance Requirements And Legal Duties
- Risks Of Inadequate Vulnerability Management
Key Takeaways
| Point | Details |
|---|---|
| Importance of Vulnerability Assessments | Conduct regular assessments to identify, quantify, and prioritize security weaknesses to comply with HIPAA. |
| Structured Methodology | Use a systematic approach to transform security data into actionable remediation strategies. |
| Integration of Assessment Types | Employ multiple assessment types, including Hazard Vulnerability Assessments and IT assessments, for comprehensive protection. |
| Consequences of Inadequate Management | Failing to manage vulnerabilities can lead to data breaches, legal penalties, and operational disruptions. |
Defining Vulnerability Assessment in Cybersecurity
A vulnerability assessment is a systematic process that identifies, quantifies, and prioritizes security weaknesses in your healthcare organization's systems, networks, and applications. Unlike vague security audits, this approach uses structured methodology to catalog what you have, determine its value, locate specific vulnerabilities, and establish mitigation priorities. The process creates a concrete inventory of where your organization stands defensively, transforming abstract security concerns into actionable intelligence that your team can address.
The core distinction lies in scope and purpose. While a vulnerability assessment process focuses on identifying and ranking weaknesses across your infrastructure, it differs from classical risk analysis by emphasizing immediate consequences and practical remediation. Your healthcare environment contains hundreds of potential entry points: patient databases, medical devices, administrative systems, wireless networks, and email servers. A vulnerability assessment examines each of these with precision, asking not just "What could go wrong?" but "What specifically needs fixing first?"
For healthcare organizations, this definition takes on regulatory urgency. Under HIPAA, you are required to conduct regular assessments of your systems handling Protected Health Information (PHI). The assessment becomes your documentation of due diligence, demonstrating to auditors that you systematically search for weaknesses rather than hoping they don't exist. Your team conducts automated scans, performs manual testing, reviews configurations, and examines access controls. The result is a detailed report that prioritizes vulnerabilities by severity and business impact, guiding your remediation roadmap.
The practical execution involves several key stages. First, you catalog what systems and assets hold or access PHI. Second, you determine which are most critical to patient care and organization operations. Third, you identify vulnerabilities specific to each asset. Finally, you rank these vulnerabilities based on severity, exploitability, and business consequence. This structured approach transforms raw vulnerability data into a strategic security improvement plan.
Pro tip: Document your vulnerability assessment methodology in writing before beginning any scans. Specify which tools you'll use, what systems you'll assess, who will validate findings, and how you'll prioritize remediation. This documentation itself satisfies HIPAA requirements and ensures consistency across assessment cycles.
Types of Vulnerability Assessments for Healthcare
Healthcare organizations employ multiple assessment approaches, each designed to address different security dimensions. The primary distinction separates assessments by what they evaluate: IT systems and networks, physical facilities, or operational hazards. Understanding which type serves your specific compliance needs prevents wasted resources and ensures your HIPAA documentation covers all required bases. Your organization likely needs more than one approach working in concert, creating overlapping layers of security evaluation.
Hazard Vulnerability Assessments (HVAs) form the foundation for many healthcare facilities. These systematic evaluations identify physical and operational risks that could disrupt patient care or compromise Protected Health Information. An HVA examines natural hazards like earthquakes and floods, human-made threats such as violence or theft, and technological failures including power outages and system crashes. Your team evaluates each hazard across multiple dimensions: probability of occurrence, impact on human safety, property damage potential, and business continuity consequences. This ranking process identifies which threats demand immediate attention and which require preventive measures. Annual reviews keep your HVA current as your facility expands, equipment changes, or community risks evolve.
IT vulnerability assessments focus specifically on your digital infrastructure and systems handling patient data. These assessments use automated scanning tools to probe network configurations, identify unpatched software, detect weak access controls, and flag misconfigurations in databases and applications. Unlike HVAs which address facility-wide threats, IT assessments zero in on the technical weaknesses that cyber attackers exploit. Your penetration testing and scanning efforts generate technical reports detailing specific vulnerabilities by severity. This data directly supports HIPAA compliance by documenting your systematic search for security gaps in systems processing PHI.

A third category involves application and data assessments, examining how specific software systems and databases store, transmit, and protect patient information. These deeper evaluations review encryption implementations, access logging, data retention practices, and backup procedures. Your assessment team works with application owners to understand data flows and identify points where PHI could be exposed or compromised.
The most effective healthcare security programs integrate all three assessment types into a coordinated schedule. HVAs address your physical and operational risks, IT assessments cover network and system vulnerabilities, and application assessments examine how specific software handles sensitive data. Together, they create comprehensive documentation of your risk identification efforts, which HIPAA requires as part of your Security Risk Assessment obligation.
Here's a comparison of vulnerability assessment types used in healthcare settings:
| Assessment Type | Main Focus | Strengths | Typical Weaknesses |
|---|---|---|---|
| Hazard Vulnerability | Physical, operational | Broad risk evaluation, regulatory fit | Less technical detail |
| IT Vulnerability | Digital infrastructure | Detailed cyber risk analysis | May ignore physical threats |
| Application & Data | Software/data handling | Deep PHI protection review | May miss facility-wide risks |
Pro tip: Schedule your HVA annually in the same quarter each year and rotate IT vulnerability scanning quarterly across different network segments. This rhythm prevents assessment fatigue while ensuring no system escapes evaluation for more than three months.
How Vulnerability Assessment Processes Work
A vulnerability assessment follows a structured workflow that transforms raw security data into actionable remediation priorities. The process works through distinct phases that build on each other: detection identifies what exists, analysis determines what matters, reporting creates organizational awareness, and remediation eliminates the identified weaknesses. This cyclical approach means your team never stops assessing because new vulnerabilities emerge constantly as systems change, patches release, and attackers develop new techniques. Understanding how each phase functions helps you allocate resources effectively and measure progress toward compliance.
The detection phase begins your assessment work. Your team deploys automated scanning tools against networks, servers, databases, and applications to identify potential weaknesses. These tools probe for missing security patches, weak password policies, open network ports, unencrypted data storage, and misconfigured access controls. Simultaneously, your team performs manual testing to catch vulnerabilities that automated tools miss. They review configuration files, examine access logs, test authentication mechanisms, and verify encryption implementations. The full vulnerability management lifecycle encompasses detection through complete remediation, creating a continuous cycle rather than a one-time event. This ongoing approach aligns with HIPAA requirements for regular assessment and continuous monitoring of systems handling Protected Health Information.
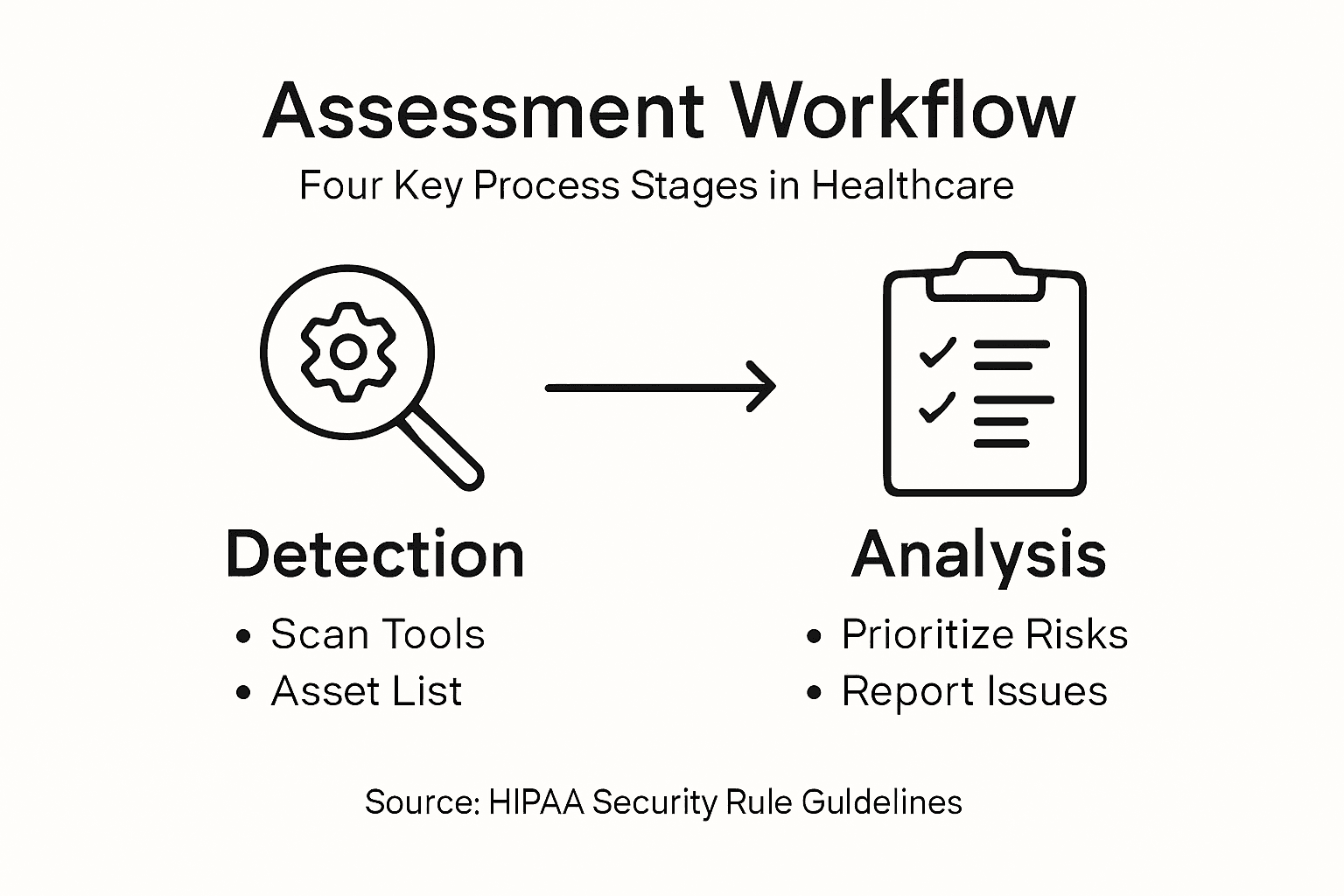
Once detection completes, the analysis phase prioritizes your findings. Not every vulnerability demands immediate attention equally. Your team assesses each identified weakness by severity (is it easily exploitable and highly damaging?), exploitability (how quickly could an attacker leverage it?), and business impact (what operations or patient care would it affect?). A vulnerability affecting a critical patient database ranks higher than one in a non-essential test system. This risk-based prioritization ensures your remediation efforts address the most dangerous gaps first. You create a prioritized list that guides your security team's work schedule and communicates to leadership which risks pose the greatest threat.
Reporting transforms technical findings into organizational communication. Your assessment team produces detailed reports documenting what was tested, what was found, how each vulnerability was assessed, and what remediation actions you recommend. This documentation becomes your HIPAA compliance evidence, proving you systematically searched for and identified security gaps. Reports circulate to system owners, IT leadership, and security stakeholders who must coordinate remediation efforts. The final phase involves actual remediation: patching systems, reconfiguring settings, replacing insecure components, or decommissioning systems that cannot be secured. After remediation completes, rescanning verifies that your fixes actually eliminated the vulnerabilities.
Below is a summary of the workflow stages in a vulnerability assessment process:
| Stage | Purpose | Key Activities |
|---|---|---|
| Detection | Identify system weaknesses | Automated scans, manual reviews |
| Analysis | Prioritize vulnerabilities | Severity rating, business impact assessment |
| Reporting | Communicate findings | Detailed documentation, recommended actions |
| Remediation | Eliminate identified weaknesses | Patch, reconfigure, or retire insecure systems |
Pro tip: Create a standard template for your vulnerability assessment reports that includes executive summaries, technical details, risk ratings, and specific remediation recommendations with responsible parties and deadlines. This consistency makes tracking progress easier and demonstrates to auditors that your assessment process follows a defined methodology.
HIPAA Compliance Requirements and Legal Duties
HIPAA imposes strict legal obligations on your healthcare organization that go far beyond general cybersecurity best practices. The law establishes federal standards protecting health information and creates enforceable duties for covered entities and their business associates. Your organization must understand that HIPAA compliance is not optional or negotiable. Violations result in substantial penalties, reputational damage, and potential criminal liability for executives. The regulation creates a framework of three interconnected rules that work together to protect patient privacy and secure sensitive health data.
The Privacy Rule governs how your organization collects, uses, discloses, and retains Protected Health Information (PHI). This rule requires you to obtain patient authorization before using their health information for purposes beyond treatment, payment, and healthcare operations. You must provide patients with access to their medical records and allow them to request corrections to inaccurate information. Your organization needs written policies explaining how PHI flows through your systems and who can access it. The Security Rule establishes specific safeguards for electronic PHI (ePHI) transmitted or stored in digital form. This is where vulnerability assessments become critical. HIPAA security safeguards encompass administrative controls like workforce training and access policies, physical controls including facility security and device management, and technical controls such as encryption and access logging. Your vulnerability assessment must examine all three categories to demonstrate you have implemented appropriate safeguards.
The Breach Notification Rule requires immediate action if PHI is exposed or compromised. You must notify affected individuals within 60 days of discovering a breach, inform the media if more than 500 individuals are affected, and report to the Department of Health and Human Services. The definition of breach is broad: any unauthorized access, use, or disclosure of PHI is presumed to be a breach unless you can prove low risk of harm. This creates urgency around addressing vulnerabilities quickly before attackers exploit them. Your vulnerability assessment documentation becomes your evidence that you conducted due diligence to prevent breaches rather than negligently ignoring known security gaps.
Your organization faces specific legal duties regarding vulnerability assessments under HIPAA's Security Rule. You must conduct a comprehensive Security Risk Assessment at least annually, identify vulnerabilities in all systems handling ePHI, and document your assessment methodology and findings. This assessment must be thorough enough to discover vulnerabilities that a reasonable healthcare organization would find. You cannot skip difficult systems or ignore inconvenient findings. If an auditor later discovers you missed vulnerabilities that your assessment should have caught, your organization faces regulatory enforcement for failing to conduct an adequate assessment. Your documentation must demonstrate not just that you scanned for vulnerabilities, but that you thought carefully about what needs assessment and why.
Pro tip: Maintain detailed assessment documentation that explicitly references which HIPAA requirements each vulnerability could violate. For example, note that unencrypted ePHI in transit violates the Transmission Security standard, or that weak access controls violate the Access Control standard. This connection between technical findings and legal obligations makes compliance clearer to leadership and auditors.
Risks of Inadequate Vulnerability Management
Healthcare organizations that fail to implement comprehensive vulnerability management programs face exponential security and financial consequences. Many organizations believe that running periodic vulnerability scans satisfies their security obligations, but scanning alone is merely the first step. Without prioritization, remediation tracking, and ongoing assessment cycles, your organization accumulates a growing backlog of unpatched systems and misconfigured defenses. Attackers systematically exploit these known weaknesses while your organization struggles to coordinate fixes across departments. The gap between identifying vulnerabilities and eliminating them becomes your organization's greatest security liability.
The most immediate risk is data breach exposure. Every unpatched vulnerability represents an open door that attackers actively search for and attempt to exploit. Healthcare data is particularly valuable on criminal markets because it includes financial information, Social Security numbers, and medical histories that enable identity theft and fraud. A single successful breach of patient data can affect thousands of individuals, triggering mandatory breach notification costs, legal liability, and regulatory enforcement. Your organization must notify affected patients, potentially fund credit monitoring services, and defend against lawsuits. Beyond immediate costs, breaches destroy patient trust and organizational reputation. A hospital known for poor security struggles to recruit talented staff and may lose patient volume as people seek care elsewhere. Inadequate vulnerability management programs leave organizations exposed to attacks exploiting unpatched systems, increasing the likelihood of costly data breaches and significant reputational damage.
Regulatory and legal consequences compound the financial impact. HIPAA enforcement actions against healthcare organizations have imposed penalties exceeding $1 million for inadequate security programs. The Department of Health and Human Services examines whether your organization conducted thorough vulnerability assessments and acted promptly to remediate findings. If auditors discover that you identified vulnerabilities during assessments but failed to address them, your organization cannot claim you took reasonable precautions. Inadequate vulnerability management becomes direct evidence of negligence. Beyond HIPAA, state breach notification laws, class action lawsuits from affected patients, and regulatory investigations by state attorneys general add layers of legal exposure. Your organization's insurance carriers may deny claims if your security practices fall below industry standards.
Operational disruption poses another significant risk. When critical systems contain unpatched vulnerabilities, attackers can encrypt files, steal data, disrupt patient care systems, or ransom your organization for payment. A ransomware attack can shut down electronic health record systems, forcing hospitals to operate using paper charts and manual processes. Patient safety suffers when clinicians cannot access medication histories or test results. Surgical procedures get canceled. Emergency departments become overwhelmed. The longer vulnerabilities persist without remediation, the greater the probability that attackers will discover and weaponize them against your specific environment. Poor vulnerability management integration into enterprise risk management allows cyber threats to evolve unchecked, risking critical organizational assets and operational resilience.
Pro tip: Establish a metrics dashboard tracking the percentage of vulnerabilities remediated within target timeframes by severity level. Present this dashboard monthly to your security leadership and quarterly to executives. Visible progress metrics motivate teams to maintain remediation momentum and alert leadership when workload bottlenecks prevent timely fixes.
Strengthen Your Healthcare Security and Achieve HIPAA Compliance Today
Navigating vulnerability assessments to ensure HIPAA compliance can be overwhelming. The challenge lies in identifying real security gaps, prioritizing risks, and maintaining thorough documentation to meet strict regulatory standards. Healthcare organizations face the critical task of protecting sensitive patient data while managing operational risks and cyber threats. With complex requirements spanning Hazard Vulnerability Assessments, IT vulnerability scans, and application security reviews, you need a trusted partner who understands these challenges deeply.
At Stonos Solutions, we specialize in comprehensive cybersecurity consulting tailored specifically for healthcare providers. Our expert team delivers in-depth security assessments and vulnerability analyses designed to uncover hidden risks and guide your remediation efforts effectively. We support you through every step of the Security Risk Assessment process required by HIPAA. By integrating advanced penetration testing, system design optimization, and compliance support, we help you transform vulnerability management from a daunting obligation into a strategic advantage.

Protect your organization from costly data breaches, operational disruption, and regulatory penalties. Take action now by partnering with Stonos Solutions to build a resilient security posture and confidently demonstrate HIPAA compliance. Visit us at Stonos Solutions to learn how our tailored services can safeguard your critical assets and improve your vulnerability management lifecycle.
Frequently Asked Questions
What is a vulnerability assessment in healthcare?
A vulnerability assessment is a systematic process that identifies, quantifies, and prioritizes security weaknesses in healthcare organizations' systems, networks, and applications to address potential risks and ensure compliance with HIPAA regulations.
How often should a healthcare organization conduct a vulnerability assessment for HIPAA compliance?
HIPAA requires healthcare organizations to conduct a comprehensive Security Risk Assessment at least annually, though many organizations benefit from more frequent assessments to stay ahead of emerging threats.
What are the main types of vulnerability assessments used in healthcare?
The main types of vulnerability assessments in healthcare include Hazard Vulnerability Assessments (HVAs), IT Vulnerability Assessments focused on digital infrastructure, and Application & Data Assessments that examine how software systems protect sensitive data.
How does a vulnerability assessment support HIPAA compliance?
A vulnerability assessment supports HIPAA compliance by systematically identifying security gaps in systems handling Protected Health Information (PHI), enabling organizations to document their due diligence and implement necessary remediation actions to protect sensitive data.
Recommended
Louis Romano
Need Security Consulting?
Our expert team is ready to help you enhance your security posture.
Contact Us Today Download Capability StatementRelated Articles
How to protect patient data in 2026: 50% fewer breaches with MFA
Discover how healthcare IT can protect patient data in 2026 with MFA, encryption, HIPAA compliance, and staff training to reduce breaches by 50%.
Read MoreRole of Penetration Testing in Industry Security
Role of penetration testing in industry security—discover core principles, testing types, compliance mandates, real-world value, and common pitfalls.
Read MoreEnterprise Security Checklist for Healthcare Compliance Success
Explore an actionable enterprise security checklist tailored for healthcare organizations. Follow a step-by-step process to ensure HIPAA compliance and risk management.
Read More