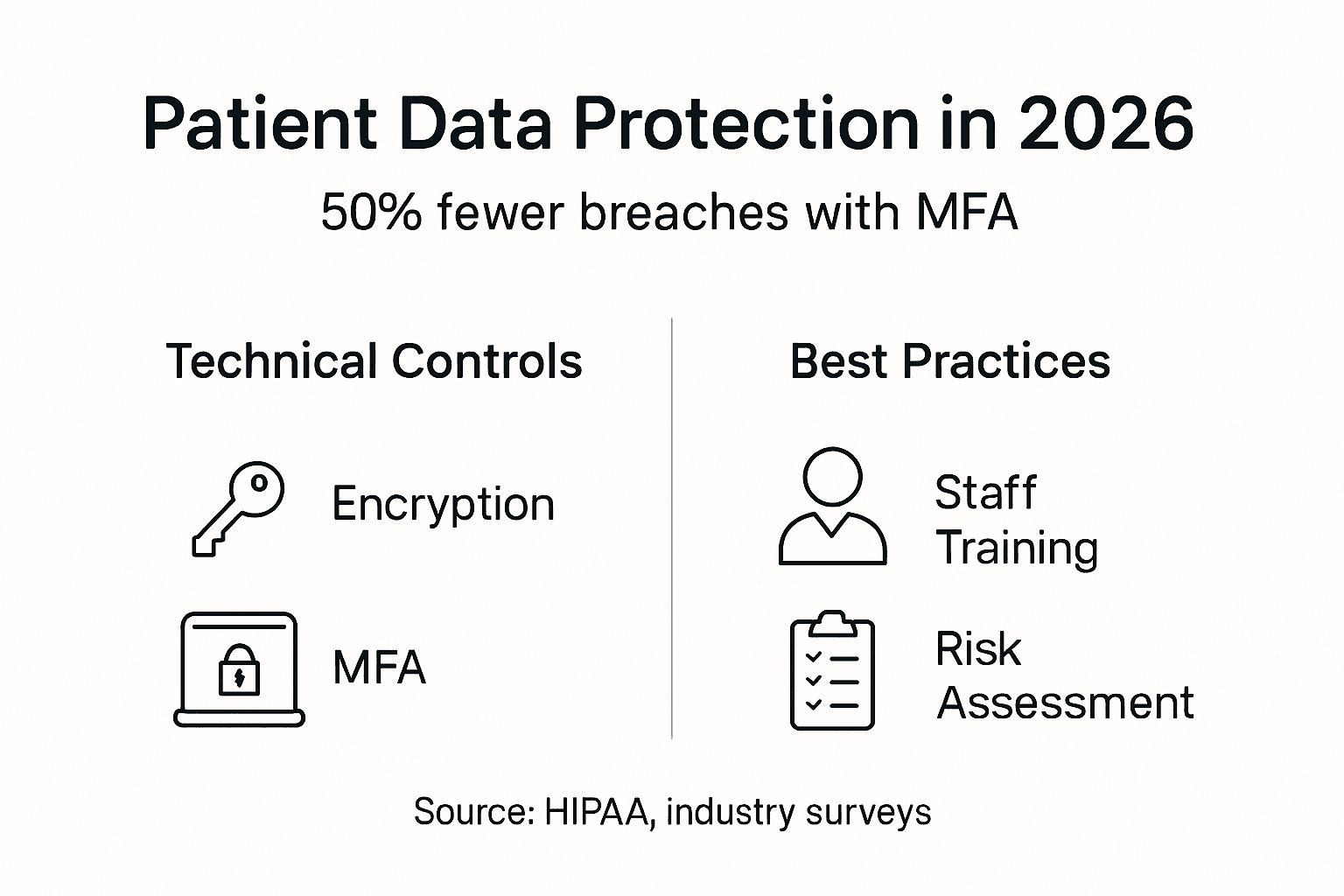
How to protect patient data in 2026: 50% fewer breaches with MFA
How to protect patient data in 2026: 50% fewer breaches with MFA

Healthcare IT professionals face an increasingly complex challenge: safeguarding patient data against sophisticated cyber threats while maintaining strict HIPAA compliance. The stakes are high, with breaches costing organizations millions and damaging patient trust irreparably. This comprehensive guide provides a structured roadmap covering technical prerequisites, implementation strategies, compliance requirements, staff training protocols, and incident response frameworks to help you build a resilient patient data protection system.
Table of Contents
- Prerequisites: What You Need Before You Start
- Technical Safeguards For Patient Data
- HIPAA Compliance Requirements And Enforcement
- Multi-Factor Authentication And Identity Management
- Staff Training And Awareness Programs
- Incident Response And Risk Management
- Cost, Timeline, And Expected Outcomes Of Security Implementations
- Common Mistakes And Troubleshooting
- Protect Patient Data With Stonos Solutions
- Frequently Asked Questions
Key takeaways
| Point | Details |
|---|---|
| Multi-factor authentication impact | MFA implementation reduces breach risk by 50%, making it the single most effective security control |
| Risk assessment frequency | Annual risk assessments improve compliance likelihood by 30% and identify vulnerabilities before exploitation |
| Access control criticality | Poor access controls cause nearly half of healthcare data breaches, making privilege management essential |
| Training effectiveness | Security training decreases incidents by 40%, transforming staff into a critical defense layer |
| Investment return | Comprehensive security investments reduce incident costs by 35%, paying for themselves through breach prevention |
Prerequisites: what you need before you start
Before implementing patient data protection measures, you need foundational elements in place. Understanding the HIPAA regulatory framework is non-negotiable. Familiarize yourself with the Security Rule's administrative, physical, and technical safeguard requirements. This knowledge guides every security decision you make.
You must have access to essential security tools. These include encryption software capable of protecting data at rest and in transit, multi-factor authentication systems, and audit logging solutions. Without these tools, implementing effective safeguards becomes impossible.
Conduct a baseline HIPAA risk assessment before making changes. Document your current infrastructure, identify existing vulnerabilities, and map data flows. This assessment reveals where patient data lives, who accesses it, and what risks threaten it.
Budget planning requires careful consideration. Allocate resources for:
- Cybersecurity software licenses and hardware tokens
- Staff training programs and compliance tracking tools
- Consulting services for specialized assessments
- Incident response planning and testing
- Ongoing monitoring and maintenance
Assemble your cybersecurity team or identify external partners who can provide expertise. You need personnel skilled in healthcare IT security, HIPAA compliance, network architecture, and incident response. If internal resources are limited, plan to engage security consulting services.
Pro Tip: Start with a comprehensive inventory of all systems that store, process, or transmit protected health information. Many breaches occur because organizations lose track of where patient data resides, including legacy systems and forgotten databases.
Technical safeguards for patient data
Technical safeguards form the foundation of robust patient data protection. Encryption of data at rest and in transit reduces unauthorized access by 95%, making it your first line of defense. Deploy AES-256 encryption for stored data and TLS 1.3 for data moving across networks.
Implement least-privilege access policies to restrict user permissions. Implementing least-privilege access policies reduces internal data leak incidents by 25%. Grant users only the minimum access required for their specific job functions. A billing clerk needs different permissions than a physician, and your access controls should reflect this reality.
Audit logging captures every interaction with patient data. Configure logs to record:
- User login attempts and access times
- Data viewing, modification, and deletion events
- System configuration changes
- Failed authentication attempts
- Privilege escalation activities
Review these logs regularly to detect suspicious patterns. Automated alerting systems can flag anomalies in real time, enabling rapid response to potential breaches.
| Security Control | Implementation Method | Protection Level |
|---|---|---|
| Encryption (rest) | AES-256 full disk encryption | Blocks 95% unauthorized access |
| Encryption (transit) | TLS 1.3 with certificate pinning | Prevents interception attacks |
| Access Control | Role-based with least privilege | Reduces internal leaks 25% |
| Audit Logging | Centralized SIEM with real-time alerts | Detects breaches within days |
Network segmentation isolates patient data from general business systems. Create separate virtual LANs for electronic health records, payment processing, and administrative functions. If attackers compromise one segment, they cannot easily pivot to sensitive patient data.
Pro Tip: Deploy endpoint detection and response (EDR) solutions on all devices accessing patient data. EDR tools identify malware, ransomware, and suspicious behavior that traditional antivirus misses, providing critical early warning of compromise.
HIPAA compliance requirements and enforcement
HIPAA compliance demands systematic attention to administrative, physical, and technical safeguards. Annual risk assessments improve compliance likelihood by 30% by identifying gaps before auditors or attackers discover them. Schedule these assessments as recurring calendar events, not one-time projects.
Follow this structured process for HIPAA risk assessments:
- Identify all locations where protected health information exists
- Evaluate current security controls against HIPAA requirements
- Assess threats and vulnerabilities specific to your environment
- Calculate risk levels based on likelihood and impact
- Document remediation plans with timelines and responsible parties
- Implement corrections and verify effectiveness
- Update your risk management plan with findings
Administrative safeguards require documented policies and procedures. Create clear written protocols for:
- Workforce security and access authorization
- Security incident response procedures
- Business associate agreements and oversight
- Training requirements and compliance tracking
- Contingency planning and disaster recovery
Common compliance failures include neglecting business associate agreements, failing to encrypt mobile devices, and inadequate access controls. Each violation carries potential penalties ranging from thousands to millions of dollars. More importantly, failures expose patients to identity theft and medical fraud.
Integrate compliance with your overall cybersecurity strategy rather than treating them separately. Security controls that protect against breaches simultaneously satisfy HIPAA requirements. For example, implementing MFA addresses both the HIPAA Security Rule's unique user identification requirement and significantly reduces breach risk.
Document everything meticulously. During audits or breach investigations, you must demonstrate compliance through written policies, training records, risk assessments, and incident logs. Thorough documentation protects your organization legally and operationally.
Understand that HIPAA sets minimum standards, not aspirational goals. Leading healthcare organizations exceed basic requirements by adopting frameworks like NIST Cybersecurity Framework. This approach provides security in IT outsourcing scenarios and strengthens overall posture.
Multi-factor authentication and identity management
MFA implementation reduces breach risk by 50%, making it the most impactful single security control you can deploy. MFA requires users to provide two or more verification factors: something they know (password), something they have (token or phone), or something they are (biometric).

Compare authentication methods to choose what fits your environment:
| MFA Type | Security Level | User Experience | Cost |
|---|---|---|---|
| SMS codes | Moderate | Convenient | Low |
| Authenticator apps | High | Very convenient | Low |
| Hardware tokens | Very high | Requires carrying device | Moderate |
| Biometric + PIN | Very high | Fast and seamless | High |
Software-based authenticators like Microsoft Authenticator or Google Authenticator offer the best balance of security and convenience. They generate time-based codes that expire quickly, preventing replay attacks. Hardware tokens provide slightly higher security but create logistical challenges if users forget or lose them.
Integrate MFA with your existing healthcare IT systems methodically. Start with high-privilege accounts like administrators, then expand to clinical users, and finally to all staff. This phased approach allows you to address integration issues before widespread deployment.
Identity management extends beyond authentication to include:
- Automated provisioning and deprovisioning based on HR systems
- Regular access reviews to remove unnecessary permissions
- Single sign-on to reduce password fatigue
- Privileged access management for administrative accounts
Implement just-in-time access for highly sensitive operations. Instead of granting permanent administrative privileges, require users to request temporary elevation that expires after a defined period. This approach minimizes the window of opportunity for credential abuse.
Pro Tip: Start MFA deployment with high-privilege accounts like system administrators and database administrators. These accounts represent the greatest risk if compromised, and securing them first provides immediate identity management best practices while you refine rollout procedures.
Staff training and awareness programs
Security training decreases incidents by 40%, transforming your workforce from a vulnerability into a defense asset. Design role-based training that addresses specific threats each employee group faces. Physicians need different guidance than billing staff or IT administrators.
Create training modules covering:
- Recognizing phishing emails and social engineering attempts
- Proper handling of patient data in digital and physical formats
- Password hygiene and MFA usage
- Reporting suspicious activity and potential breaches
- Mobile device security and remote access protocols
Schedule training at hire, annually thereafter, and whenever significant security changes occur. New employees must complete training before accessing patient data. Annual refreshers reinforce concepts and introduce emerging threats.
Use compliance tracking tools to monitor training completion rates. Generate reports showing which staff members have completed required modules and which need follow-up. Tie training completion to access privileges, automatically suspending accounts for non-compliant users.
Phishing simulations provide practical experience recognizing attacks. Send simulated phishing emails monthly and track who clicks suspicious links or provides credentials. Users who fail simulations receive immediate additional training. Over time, click rates drop dramatically as awareness improves.
Measure training effectiveness through:
- Pre and post-training knowledge assessments
- Phishing simulation click rates over time
- Security incident reports attributed to human error
- Time to detect and report suspicious activity
Make training engaging rather than tedious. Use real-world examples from healthcare breaches, interactive scenarios, and short videos instead of lengthy text documents. Staff who find training relevant and interesting retain information better.
Pro Tip: Include phishing simulations in your training program to reinforce concepts through practice. Employees who experience realistic simulated attacks become far more cautious with actual phishing attempts, dramatically reducing successful compromise rates.
Incident response and risk management
Continuous monitoring can detect breaches on average within 5 days, compared to months for organizations relying on periodic reviews. Deploy security information and event management (SIEM) systems that aggregate logs from all sources and apply correlation rules to identify suspicious patterns.
Develop and test a formal incident response plan before you need it. Your plan should define:
- Detection and analysis procedures for identifying potential incidents
- Containment strategies to prevent breach expansion
- Eradication steps to remove threats from your environment
- Recovery processes to restore normal operations
- Post-incident review to improve future response
- Notification requirements for patients, regulators, and law enforcement
Test your incident response plan through tabletop exercises quarterly. Simulate various scenarios like ransomware attacks, insider threats, or third-party breaches. These exercises reveal gaps in your procedures and prepare your team to respond effectively under pressure.
Third-party vendor risks require proactive management. Your business associates can become entry points for attackers targeting your patient data. Implement vendor risk management by:
- Requiring security assessments before contract signing
- Including specific security requirements in business associate agreements
- Conducting periodic audits of vendor security practices
- Monitoring vendor security incidents that could affect your data
- Maintaining an inventory of all vendors with patient data access
Deploy incident detection tools that provide real-time alerting. Configure alerts for high-risk activities like multiple failed login attempts, unusual data access patterns, or changes to security configurations. Immediate notification enables rapid response before minor incidents escalate into major breaches.
Maintain cyber insurance coverage appropriate to your risk profile. Insurance cannot prevent breaches, but it mitigates financial impact by covering forensic investigations, legal fees, notification costs, and regulatory fines. Review policy terms carefully to understand coverage limits and exclusions.
Cost, timeline, and expected outcomes of security implementations
Typical HIPAA risk assessment and remediation projects span 6 to 9 months from initial assessment through full implementation of corrective measures. Rush implementations often miss critical details, while projects extending beyond 9 months lose momentum and executive support.
Healthcare cybersecurity investments reduce incident costs by 35%, providing clear return on investment. A single major breach can cost millions in forensic investigation, legal fees, regulatory fines, and reputation damage. Prevention costs a fraction of breach remediation.
| Security Initiative | Typical Cost Range | Implementation Time | Expected Outcome |
|---|---|---|---|
| HIPAA risk assessment | $15,000 - $50,000 | 6-8 weeks | Compliance roadmap, vulnerability identification |
| MFA deployment | $20,000 - $75,000 | 3-4 months | 50% reduction in breach risk |
| Encryption implementation | $30,000 - $100,000 | 4-6 months | 95% reduction in unauthorized access |
| Staff training program | $10,000 - $40,000 annually | Ongoing | 40% decrease in security incidents |
| SIEM and monitoring | $50,000 - $200,000 | 6-8 months | Breach detection within 5 days |
Budget for three major cost categories. Technology costs include software licenses, hardware, and infrastructure upgrades. Personnel costs cover security staff salaries or consulting fees. Training costs encompass program development, delivery, and compliance tracking.
Define success metrics that demonstrate security improvement:
- Reduction in successful phishing attacks
- Faster breach detection and response times
- Improved audit scores and compliance ratings
- Decreased number of access control violations
- Lower cyber insurance premiums
Many organizations benefit from understanding IT outsourcing trends when planning security implementation costs. Managed security service providers can deliver enterprise-grade protection at lower costs than building internal capabilities.
Plan for ongoing operational costs beyond initial implementation. Security requires continuous monitoring, regular updates, staff training refreshers, and periodic assessments. Budget 15 to 20 percent of initial implementation costs annually for maintenance and improvements.
Common mistakes and troubleshooting
Neglecting timely software patches increases ransomware risk by 33%. Attackers exploit known vulnerabilities that patches address. Implement automated patch management systems that test and deploy updates systematically. Prioritize patches for internet-facing systems and those processing patient data.
Underestimating incident response planning leaves organizations scrambling during breaches. Without tested procedures, response teams waste critical time deciding who does what. This confusion allows attacks to spread and increases damage. Develop, document, and practice your incident response plan regularly.
Failing to manage third-party vendor security risks creates blind spots in your security posture. Your vendors may have weaker security than your organization, making them attractive targets. Attackers compromise vendors to gain access to your patient data indirectly.
Common troubleshooting scenarios include:
- MFA causing workflow disruptions: Implement single sign-on to reduce authentication frequency
- Encryption slowing system performance: Upgrade hardware or optimize encryption methods
- Staff resistance to security changes: Improve training to explain why measures protect patients
- Alert fatigue from too many false positives: Tune monitoring rules to reduce noise
- Budget constraints limiting security investments: Prioritize highest-risk areas first
Overlooking mobile device security exposes patient data when staff access systems remotely. Require mobile device management (MDM) solutions that enforce encryption, remote wipe capabilities, and security policies. Lost or stolen devices should not result in data breaches.
Ignoring security in legacy systems creates vulnerabilities. Older systems may lack encryption, proper authentication, or logging capabilities. If you cannot upgrade immediately, isolate legacy systems on separate network segments and implement compensating controls.
Pro Tip: Automate patch management to avoid delays that expose you to known vulnerabilities. Configure systems to test patches in a staging environment, then deploy automatically to production on a defined schedule, ensuring critical security updates happen promptly.
Protect patient data with Stonos Solutions
Implementing comprehensive patient data protection requires specialized expertise in healthcare security and HIPAA compliance. Stonos Solutions delivers tailored security services designed specifically for healthcare organizations facing complex cybersecurity challenges. Our team conducts thorough HIPAA risk assessments that identify vulnerabilities and provide actionable remediation roadmaps.

We offer penetration testing, system design optimization, and security consulting that transforms your security posture from reactive to proactive. Our expertise spans technical safeguards, compliance frameworks, staff training programs, and incident response planning. Whether you need a comprehensive security assessment or targeted improvements to specific controls, Stonos Solutions provides the guidance and implementation support to protect your patient data effectively. Contact us to discuss how we can strengthen your healthcare security program.
Frequently asked questions
How can healthcare IT protect patient data effectively?
Effective patient data protection combines multiple layers: technical safeguards like encryption and MFA, comprehensive staff training programs, continuous monitoring for threats, and regular HIPAA compliance assessments. No single measure provides complete protection. You need defense in depth that addresses technology, processes, and people. Start with high-impact controls like MFA and encryption, then expand to monitoring and training.
What are the biggest vulnerabilities in healthcare data security?
Poor access controls, unpatched software, and third-party vendor risks represent the most significant vulnerabilities. Nearly half of breaches stem from inadequate access management. Unpatched systems provide easy entry points for ransomware and other malware. Vendors with weak security can become backdoors into your network. Addressing these three areas dramatically reduces your breach likelihood.
How often should healthcare organizations conduct risk assessments?
Conduct formal risk assessments at least annually or whenever significant system changes occur. Annual assessments identify new vulnerabilities introduced through technology changes, new threats, or procedural modifications. Major changes like implementing new EHR systems, opening new facilities, or adding business associates require immediate targeted assessments. Continuous monitoring supplements periodic formal assessments.
What role does staff training play in patient data protection?
Well-trained staff reduce security incidents by 40% by recognizing and avoiding common attack vectors. Employees who understand phishing tactics, proper data handling procedures, and reporting requirements become active participants in your security program. Ongoing education creates a security-aware culture where staff view protection as everyone's responsibility, not just the IT department's job.
Recommended
- How to Conduct Security Risk Assessment for HIPAA Compliance - Stonos Solutions Blog
- Top 7 Penetration Testing Tools for Small Business 2026 - Stonos Solutions Blog
- Blog - Security Insights & Industry News - Stonos Solutions
- Security Consulting for Integrators: Enabling Resilience - Stonos Solutions Blog
Louis Romano
Need Security Consulting?
Our expert team is ready to help you enhance your security posture.
Contact Us Today Download Capability StatementRelated Articles
Security gap analysis: steps, benefits, and best practices
Learn how to conduct a security gap analysis to identify hidden risks, close compliance gaps, and build a stronger security posture in regulated industries.
Read MoreEnterprise Security Checklist for Healthcare Compliance Success
Explore an actionable enterprise security checklist tailored for healthcare organizations. Follow a step-by-step process to ensure HIPAA compliance and risk management.
Read More7 Key Types of Cybersecurity Assessments for Healthcare
Learn about 7 essential types of cybersecurity assessments for healthcare organizations and get actionable tips to boost compliance and security.
Read More