Cyber Risk Analysis: Shaping Secure Healthcare Futures
Cyber Risk Analysis: Shaping Secure Healthcare Futures
Healthcare organizations across the United States face increasing pressure to protect sensitive patient data and safeguard clinical systems as their technological environments become more complex. Cyber risks threaten not only operational continuity but also patient safety, with vulnerabilities stemming from interconnected medical devices and cloud adoption. For cybersecurity managers aiming to strengthen compliance and build real resilience, a comprehensive cyber risk analysis framework is pivotal for identifying and closing potential security gaps before they escalate.
Table of Contents
- Defining Cyber Risk Analysis in Healthcare
- Categories of Cyber Risks and Threat Profiles
- The Cyber Risk Assessment Lifecycle Explained
- Regulatory Standards Impacting Risk Analysis
- Common Pitfalls and Mitigation Strategies
Key Takeaways
| Point | Details |
|---|---|
| Cyber Risk Analysis Importance | A strategic approach is essential for identifying vulnerabilities in healthcare to protect patient data and maintain operational integrity. |
| Dynamic Risk Assessment | Regular assessments and updates are critical to adapt to emerging threats in the evolving healthcare technology landscape. |
| Comprehensive Cybersecurity Strategy | A holistic approach addressing technical, human, and organizational risks will enhance resilience against cyber threats. |
| Regulatory Compliance as Foundation | Integrating regulatory standards into operations not only ensures compliance but strengthens overall cybersecurity practices. |
Defining Cyber Risk Analysis in Healthcare
Cyber risk analysis in healthcare represents a strategic approach to understanding and mitigating digital vulnerabilities that could compromise patient data, clinical systems, and organizational operations. At its core, this process involves systematically identifying, evaluating, and addressing potential cybersecurity threats unique to medical environments.
Healthcare organizations face increasingly complex cyber risks due to their intricate technological ecosystems. Cybersecurity challenges in interconnected medical systems highlight the critical need for comprehensive risk assessment strategies. These challenges emerge from multiple interconnected sources:
- Sensitive patient health records
- Networked medical devices
- Cloud-based storage systems
- Complex digital health infrastructure
- Interoperability between different healthcare platforms
The primary objective of cyber risk analysis is to create a robust framework that proactively identifies potential security gaps before they can be exploited. This involves a multifaceted approach that goes beyond traditional security measures, requiring deep understanding of healthcare-specific technological landscapes and potential vulnerabilities.
Effective cyber risk analysis transforms potential technological weaknesses into strategic organizational strengths.
Healthcare cybersecurity differs significantly from other industries due to the direct impact on patient safety and critical care delivery. Cyber risks affecting clinical service preparedness underscore the importance of developing tailored risk management strategies that account for the unique demands of medical technology environments.
Pro tip: Conduct regular comprehensive cyber risk assessments that simulate real-world attack scenarios specific to healthcare technology infrastructures.
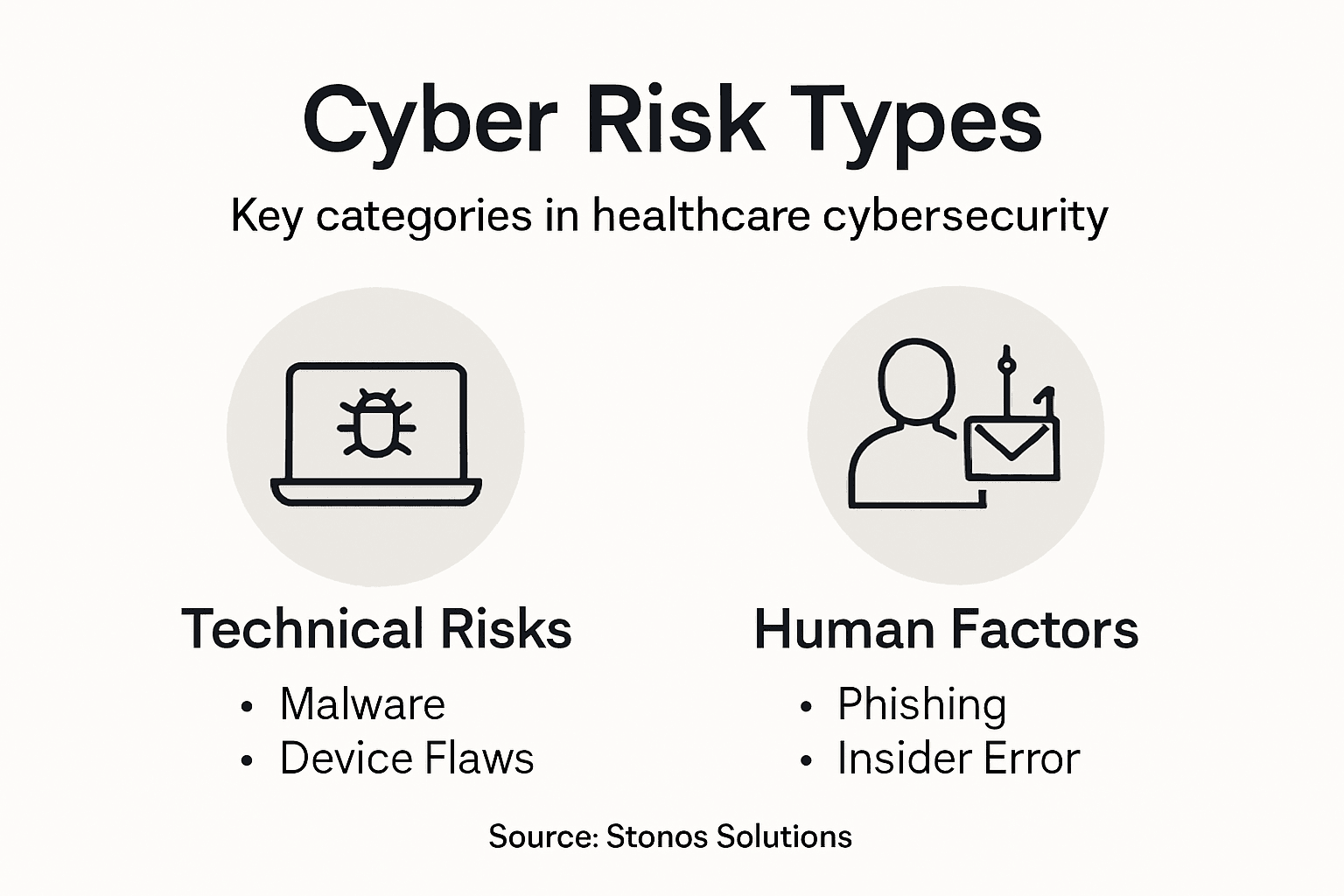
Categories of Cyber Risks and Threat Profiles
Healthcare cybersecurity encompasses a complex landscape of digital threats that require nuanced understanding and strategic management. Comprehensive threat profiles in healthcare reveal multiple categories of risks that can compromise patient data, clinical systems, and organizational integrity.
Cyber risks in healthcare can be broadly categorized into several critical domains:
- Technical Vulnerabilities:
- Software bugs and misconfigurations
- Unpatched system weaknesses
- Network infrastructure gaps
-
Outdated medical device firmware
-
Human Factor Risks:
- Social engineering attacks
- Insider threats
- Insufficient staff cybersecurity training
-
Accidental data exposure
-
Organizational Risks:
- Inadequate access controls
- Poor incident response planning
- Fragmented security governance
- Limited cybersecurity investment
Advanced persistent threats targeting healthcare represent particularly sophisticated challenges that demand comprehensive defense strategies. These complex attack vectors often involve multi-stage infiltration techniques designed to penetrate healthcare networks undetected, potentially compromising sensitive patient information and critical medical systems.
Effective cybersecurity in healthcare requires a holistic approach that anticipates and neutralizes threats across technical, human, and organizational domains.
Threat actors range from individual hackers to organized cybercrime groups and even nation-state sponsored entities, each with distinct motivations and sophisticated attack methodologies. Understanding these diverse threat profiles enables healthcare organizations to develop targeted, proactive defense mechanisms that protect patient data and maintain operational continuity.
Here's a summary of common healthcare cyber risk categories, how they impact organizations, and recommended methods for reducing these risks:
| Risk Category | Organizational Impact | Mitigation Approach |
|---|---|---|
| Technical Vulnerabilities | Disruption of clinical operations | Regular system updates and patching |
| Human Factor Risks | Unauthorized access to patient data | Ongoing staff training |
| Organizational Risks | Inadequate response to incidents | Establish incident management protocols |
Pro tip: Develop a dynamic threat intelligence framework that continuously maps emerging cyber risks specific to healthcare technological ecosystems.
The Cyber Risk Assessment Lifecycle Explained
The cyber risk assessment lifecycle represents a strategic, systematic approach to identifying, evaluating, and mitigating potential cybersecurity threats within healthcare organizations. Comprehensive risk assessment framework provides healthcare institutions with a structured methodology to proactively manage digital vulnerabilities and protect critical systems.
The lifecycle typically encompasses several critical stages:
- Asset Identification and Inventory:
- Catalog all digital and physical assets
- Map interconnected medical systems
- Document hardware and software configurations
-
Identify data flow and storage mechanisms
-
Vulnerability Assessment:
- Scan systems for potential weaknesses
- Review software patch levels
- Analyze network configurations
-
Evaluate access control mechanisms
-
Threat Evaluation:
- Identify potential threat actors
- Assess likelihood of attacks
- Analyze potential impact scenarios
-
Prioritize risk mitigation strategies
-
Risk Mitigation Planning:
- Develop targeted remediation strategies
- Implement security controls
- Create incident response protocols
- Establish continuous monitoring mechanisms
Risk and vulnerability assessment practices emphasize the importance of treating cyber risk assessment as a dynamic, ongoing process rather than a one-time event. Healthcare organizations must continuously adapt their strategies to address emerging threats and technological changes.
Effective cyber risk assessment is not a destination, but a continuous journey of adaptation and improvement.
Successful implementation requires cross-functional collaboration, integrating insights from IT, clinical operations, compliance, and leadership teams. This holistic approach ensures that risk assessment strategies align with both technological capabilities and organizational objectives.

Pro tip: Implement a quarterly review cycle that reassesses your cyber risk landscape, incorporating the latest threat intelligence and technological developments.
Regulatory Standards Impacting Risk Analysis
Healthcare cybersecurity is fundamentally shaped by a complex framework of regulatory standards that establish critical benchmarks for data protection and risk management. Cybersecurity best practices for healthcare provide a comprehensive guide to understanding the intricate landscape of compliance requirements that healthcare organizations must navigate.
Key regulatory standards impacting cyber risk analysis include:
- HIPAA Security Rule:
- Mandates protected health information (PHI) safeguards
- Requires risk assessment and management protocols
- Establishes minimum security standards
-
Defines breach notification requirements
-
NIST Cybersecurity Framework:
- Provides risk management guidelines
- Offers standardized approach to cybersecurity
- Supports continuous improvement
-
Enables cross-organizational communication
-
HITECH Act:
- Strengthens data privacy protections
- Increases penalties for data breaches
- Promotes electronic health record security
- Expands HIPAA enforcement capabilities
These regulatory standards collectively create a robust framework that compels healthcare organizations to develop sophisticated, proactive cyber risk analysis strategies. They do not merely represent compliance checkboxes but serve as critical blueprints for comprehensive cybersecurity management.
Regulatory compliance is the foundation upon which effective cybersecurity strategies are constructed.
Successful implementation requires more than surface-level adherence. Healthcare organizations must integrate these standards into their core operational processes, transforming regulatory requirements into genuine security practices that protect patient data and maintain organizational resilience.
A quick reference table comparing major healthcare cybersecurity regulations and what each requires:
| Regulation | Focus Area | Key Requirement | Enforcement Method |
|---|---|---|---|
| HIPAA Security Rule | Patient data protection | Safeguard health information | Federal audits and penalties |
| NIST Framework | Risk management process | Structured security controls | Voluntary adoption, industry norms |
| HITECH Act | Data breach accountability | Increase breach reporting | Enhanced penalties, oversight |
Pro tip: Develop a cross-functional compliance team that translates regulatory requirements into actionable cybersecurity strategies.
Common Pitfalls and Mitigation Strategies
Healthcare cybersecurity requires understanding the nuanced landscape of potential vulnerabilities that can compromise patient data and organizational integrity. Key risk and vulnerability findings reveal critical systemic weaknesses that demand strategic and comprehensive mitigation approaches.
Common cybersecurity pitfalls in healthcare organizations include:
- Technical Vulnerabilities:
- Outdated software systems
- Unpatched network infrastructure
- Misconfigured security settings
- Legacy medical device weaknesses
-
Inadequate network segmentation
-
Operational Risks:
- Insufficient staff cybersecurity training
- Weak access control mechanisms
- Poor incident response planning
- Decentralized security management
-
Limited visibility into system vulnerabilities
-
Human Factor Challenges:
- Social engineering susceptibility
- Inconsistent security protocol adherence
- Limited cybersecurity awareness
- Unauthorized device usage
- Inadequate password management practices
Comprehensive cybersecurity strategies emphasize that effective mitigation requires a holistic approach addressing technological, operational, and human dimensions of cybersecurity risk.
Successful cyber risk mitigation transforms vulnerabilities into opportunities for organizational resilience and strategic improvement.
Healthcare organizations must develop adaptive, proactive strategies that continuously evolve with emerging technological landscapes. This involves creating robust frameworks that integrate technical controls, ongoing education, and dynamic risk assessment methodologies.
Pro tip: Establish a continuous learning cybersecurity program that combines technical training, simulated threat scenarios, and regular vulnerability assessments.
Strengthen Your Healthcare Cybersecurity With Expert Risk Analysis
Healthcare organizations face complex cyber risks that threaten patient safety and critical operations. The urgent need for comprehensive cyber risk analysis spans technical vulnerabilities, human factor challenges, and regulatory compliance demands such as HIPAA and NIST frameworks. At Stonos Solutions, we understand the high stakes involved in protecting sensitive data and clinical systems amid evolving threats. Our tailored security assessments and vulnerability analyses transform potential weaknesses into resilient defenses designed specifically for healthcare environments.

Take control of your cybersecurity future by partnering with a trusted veteran-owned firm. Explore how Stonos Solutions delivers risk management strategies, penetration testing, and compliance support that align with your organization's unique needs. Don't wait for a breach to act. Visit Stonos Solutions today to schedule a consultation and safeguard your healthcare infrastructure now. Learn more about our comprehensive cybersecurity consulting services and discover collaboration opportunities with our expert team.
Frequently Asked Questions
What is cyber risk analysis in healthcare?
Cyber risk analysis in healthcare is a strategic approach to identify, evaluate, and mitigate cybersecurity threats that could compromise patient data, clinical systems, and overall organizational operations.
Why are healthcare organizations particularly vulnerable to cyber risks?
Healthcare organizations face unique vulnerabilities due to sensitive patient data, interconnected medical devices, cloud storage, and complex digital infrastructures, all of which present opportunities for cyberattacks.
What are the common categories of cyber risks in healthcare?
Common categories of cyber risks in healthcare include technical vulnerabilities (like software bugs), human factor risks (such as social engineering), and organizational risks (like inadequate access controls).
How can healthcare organizations effectively mitigate cyber risks?
Healthcare organizations can mitigate cyber risks by conducting regular vulnerability assessments, providing ongoing staff cybersecurity training, developing incident response protocols, and continuously adapting their cybersecurity strategies based on emerging threats.
Recommended
- How to Conduct Security Risk Assessment for HIPAA Compliance - Stonos Solutions Blog
- Top 7 Penetration Testing Tools for Small Business 2026 - Stonos Solutions Blog
- Security Consulting for Integrators: Enabling Resilience - Stonos Solutions Blog
- Services for End Users - Stonos Solutions
- Healthcare Data Security: Best Practices & Tips | SingleClic
Louis Romano
Need Security Consulting?
Our expert team is ready to help you enhance your security posture.
Contact Us Today Download Capability StatementRelated Articles
Security gap analysis: steps, benefits, and best practices
Learn how to conduct a security gap analysis to identify hidden risks, close compliance gaps, and build a stronger security posture in regulated industries.
Read MoreEnterprise Security Checklist for Healthcare Compliance Success
Explore an actionable enterprise security checklist tailored for healthcare organizations. Follow a step-by-step process to ensure HIPAA compliance and risk management.
Read More7 Key Types of Cybersecurity Assessments for Healthcare
Learn about 7 essential types of cybersecurity assessments for healthcare organizations and get actionable tips to boost compliance and security.
Read More