Security gap analysis: steps, benefits, and best practices
Security gap analysis: steps, benefits, and best practices

TL;DR:
- Security gap analysis compares current controls against industry standards to identify vulnerabilities.
- It is essential for risk management and continuous improvement beyond compliance audits.
- Proper integration and executive ownership ensure effective remediation and organizational security posture.
Passing a compliance audit feels like a win. But compliance and security are not the same thing, and regulated organizations learn this the hard way when breaches occur despite holding valid certifications. Over 80% of breached organizations were considered compliant at the time of the incident. A security gap analysis cuts through that false confidence by mapping exactly where your defenses fall short against proven standards. This guide walks security managers and IT executives through what a gap analysis is, how to run one, and how to turn findings into lasting protection.
Table of Contents
- Understanding security gap analysis
- The security gap analysis process: step by step
- From findings to action: closing security gaps
- Business impact and industry best practices
- Why security gap analysis fails and how to do it right
- Take your gap analysis further with the right partner
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Beyond compliance | Security gap analysis reveals risks compliance checks miss, reducing real-world threats. |
| Structured, repeatable process | Effective gap analysis follows a clear method aligned to business and regulatory priorities. |
| Lasting business value | When integrated with risk management, gap analysis enables smarter investment and asset protection. |
| Continuous improvement | Closing security gaps is an ongoing effort tied to metrics, stakeholder buy-in, and evolving threats. |
Understanding security gap analysis
A security gap analysis is a structured evaluation that compares your organization's current security controls against recognized industry standards and best practices. As defined by NIST IR 8286B, it is "a structured process that compares current security controls with industry standards and best practices." The output is a clear picture of where you stand today versus where you need to be.
Many security leaders confuse gap analysis with a compliance audit. They are related but distinct. A compliance audit checks whether you meet a specific regulatory threshold at a point in time. A gap analysis is broader: it examines your actual risk exposure, control effectiveness, and alignment with frameworks like NIST, ISO 27001, HIPAA, and PCI DSS. Understanding the difference between compliance vs security is the first step toward building a program that actually protects your organization.
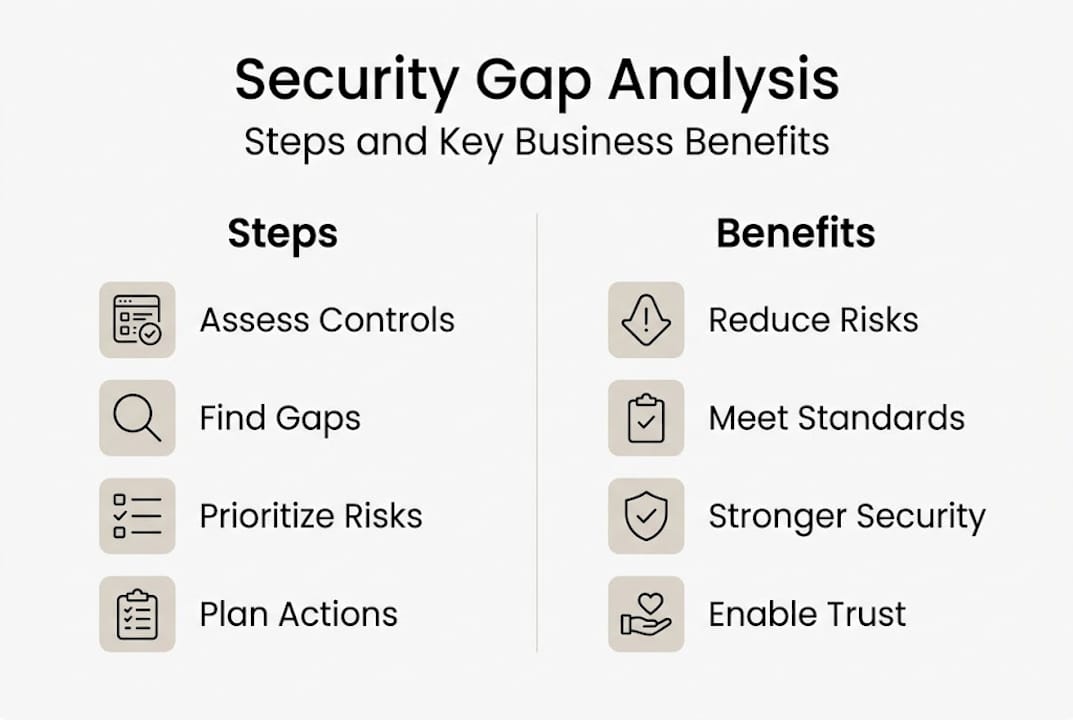
The core goals of a security gap analysis are:
- Risk identification: Surface vulnerabilities that audits may not catch
- Prioritization: Rank gaps by severity and business impact
- Actionable improvement: Produce a remediation roadmap with clear owners
- Regulatory alignment: Confirm controls meet or exceed required standards
Here is a quick comparison to clarify the distinction:
| Attribute | Compliance audit | Security gap analysis |
|---|---|---|
| Scope | Specific regulation | Broad security posture |
| Frequency | Scheduled/annual | Ongoing or triggered |
| Output | Pass/fail result | Prioritized gap list |
| Focus | Minimum standards | Best practice alignment |
| Business alignment | Limited | High |
In regulated sectors such as healthcare, government, and manufacturing, a gap analysis is not optional. Regulatory bodies increasingly expect organizations to demonstrate continuous risk awareness, not just periodic compliance. Integrating risk analysis into your security program from the start ensures that gap findings drive real decisions rather than sitting in a report.
Pro Tip: Treat your gap analysis as a living document. Update it whenever you deploy new systems, onboard major vendors, or experience a regulatory change. Static reports go stale fast.
With the basics in mind, let's see how the security gap analysis process actually unfolds in a real-world organization.
The security gap analysis process: step by step
A well-run gap analysis follows a repeatable structure. Improvising the process leads to inconsistent findings and weak remediation plans. Here is how to do it right.
- Define scope and objectives. Identify which systems, business units, and regulatory frameworks are in scope. Narrow scope produces faster results; broad scope produces more complete ones. Match scope to your risk appetite and available resources.
- Assemble the right stakeholders. Include IT security, compliance, legal, operations, and executive sponsors. Each group brings a different view of risk. Missing any one of them creates blind spots.
- Gather current-state data. Collect existing policies, system configurations, audit logs, incident reports, and prior assessments. This is your baseline. Without it, you are guessing.
- Assess current controls. Evaluate each control against your chosen framework. Use interviews, documentation review, and technical testing. Penetration testing tools can validate whether technical controls actually work under pressure.
- Map findings against standards. For each control area, document the current state, the target state, and the gap between them. Be specific. Vague gaps produce vague fixes.
- Prioritize and document. Assign severity ratings and business impact scores to each gap. This drives your remediation roadmap.
Here is a sample gap tracking table:
| Gap category | Severity | Business impact | Priority |
|---|---|---|---|
| Access control | High | Data exposure | Immediate |
| Patch management | Medium | System compromise | 30 days |
| Incident response | High | Operational disruption | Immediate |
| Security awareness training | Low | Human error risk | 90 days |
| Encryption standards | Medium | Regulatory penalty | 60 days |
As NIST IR 8286B states, gap analysis should be integrated into enterprise risk management (ERM) for prioritizing assets and directing responses. This means your gap findings should feed directly into your broader IT security risk strategies, not exist as a standalone exercise.

Pro Tip: Use a HIPAA risk assessment as a model even if you are not in healthcare. Its structured approach to identifying, categorizing, and scoring risks translates well to any regulated environment.
Once the process is clear, it's important to see how results turn into prioritized action.
From findings to action: closing security gaps
A gap analysis report is only valuable if it drives change. Many organizations produce detailed findings and then watch them collect dust. Turning findings into action requires structure, ownership, and executive commitment.
Start by categorizing your gaps into three tiers:
- Immediate action (0 to 30 days): Critical vulnerabilities with high breach likelihood or regulatory penalty exposure
- Short-term action (30 to 90 days): Significant gaps that require policy updates, technical controls, or training programs
- Long-term action (90 to 180 days): Process improvements, system redesigns, and vendor management updates
For each gap, assign a named owner, a target completion date, and a success metric. Ambiguous ownership is the single biggest reason remediation stalls. If no one is accountable, nothing gets fixed.
Common remediation actions include:
- Updating access control policies and reviewing user privilege levels
- Deploying multi-factor authentication across critical systems
- Conducting targeted security awareness training for high-risk roles
- Patching or replacing end-of-life systems identified during the assessment
- Revising incident response plans to reflect current threat scenarios
Tracking progress matters as much as the initial remediation. Use key performance indicators (KPIs) such as percentage of critical gaps closed, mean time to remediate, and recurring vulnerability rates. These metrics give executives a clear view of program health and justify continued investment. Review security compliance tips to build KPI frameworks that align with regulatory expectations.
Executive sponsorship is not optional. Without visible leadership support, security teams lack the authority and budget to close gaps that require cross-departmental cooperation. Tie each remediation task to a business outcome, such as reduced breach risk, lower insurance premiums, or avoided regulatory fines. That language resonates in boardrooms.
Regularly addressing identified security gaps dramatically reduces breach likelihood in regulated sectors. Pairing your remediation roadmap with risk management tactics ensures that closed gaps stay closed and new ones get caught early.
The value of gap analysis is even more apparent when we look at its impact at the organizational level.
Business impact and industry best practices
Security gap analysis is not just a technical exercise. For regulated industries, it is a business continuity tool. Organizations that treat it as such see measurably better outcomes.
Consider how different sectors benefit:
- Healthcare: Hospitals and health systems use gap analysis to align with HIPAA and HITECH requirements, protecting patient data and avoiding seven-figure fines
- Financial services: Banks and payment processors use it to meet PCI DSS and SOX requirements while reducing fraud exposure
- Manufacturing: Industrial operators identify gaps in operational technology (OT) security, protecting production lines from ransomware and sabotage. Reviewing manufacturing security gaps reveals how often physical and cyber risks intersect in this sector
- Government contractors: Federal agencies and their vendors use gap analysis to meet FISMA and CMMC requirements, protecting sensitive national security data
Best practice frameworks that inform effective gap analysis include NIST Cybersecurity Framework (CSF), NIST SP 800-53, ISO 27001, and COBIT. Each provides a structured control catalog you can map your current state against.
"Organizations using gap analysis as an ongoing ERM activity see better asset protection and strategic response capabilities." — NIST IR 8286B
To make gap analysis business-relevant, tie findings to your Business Impact Analysis (BIA). When a gap directly threatens a revenue-generating process or a critical compliance obligation, it moves up the priority list and gets funded. Executives respond to business risk language, not technical jargon.
Pitfalls to avoid include treating gap analysis as a one-time event, running it in isolation from ERM, and failing to coordinate remediation across departments. Uncoordinated fixes often create new gaps elsewhere. Custom security automation can help organizations scale their gap monitoring and remediation tracking without adding headcount. The data breach risks facing organizations today make a continuous, integrated approach non-negotiable.
Finally, let's examine our perspective on what organizations often get wrong in their approach to security gap analysis and how to avoid it.
Why security gap analysis fails and how to do it right
Here is something most security vendors won't tell you: the majority of gap analyses fail not because of poor methodology, but because of poor integration. Organizations conduct thorough assessments, produce detailed reports, and then file them away until the next audit cycle. The analysis becomes a compliance artifact rather than a management tool.
The real problem is that gap findings are rarely connected to business objectives. When a remediation task lacks a clear link to revenue protection, regulatory risk, or operational continuity, it loses the competition for budget and attention. Security teams know this pattern well.
The fix is straightforward but requires discipline. Every gap finding should map to a specific business risk. Every remediation task should have an executive owner, not just a technical one. And the entire process should feed into your ERM cycle, not run parallel to it. Our security consulting perspective on this is consistent: organizations that align security gaps with business impact get remediation funded and completed. Those that don't, repeat the same findings year after year.
With practical strategies for lasting improvement in mind, here's how we can help you take the next step.
Take your gap analysis further with the right partner
Understanding your security gaps is the first step. Acting on them with precision is where most organizations need support. Stonos Solutions works with security managers and IT executives in regulated industries to move from gap findings to measurable, documented security improvements.

Our team brings CISSP-certified expertise across healthcare, government, manufacturing, and enterprise environments. From penetration testing services that validate your technical controls to tailored risk remediation roadmaps, we help you close gaps that matter most. Explore our full range of security services to find the right starting point for your organization's security posture. Contact Stonos Solutions today to schedule a consultation.
Frequently asked questions
What is the main purpose of a security gap analysis?
A security gap analysis identifies differences between your current safeguards and established best practices, giving you a prioritized roadmap to improve both security and compliance. Gap analysis is fundamental for identifying risks and aligning with security standards.
How often should regulated organizations perform a security gap analysis?
Regulated organizations should conduct a gap analysis at least annually or after any significant system change, major regulatory update, or security incident. Ongoing gap analysis is required for strong risk management and sustained compliance.
What standards or frameworks inform a security gap analysis?
A security gap analysis commonly uses NIST CSF, NIST SP 800-53, ISO 27001, HIPAA, PCI DSS, or FISMA as benchmarks depending on your industry. Best practice frameworks such as NIST provide structured control catalogs that make gap identification systematic and defensible.
Who should lead a security gap analysis effort?
A cross-functional team led by IT or security management, with participation from compliance, legal, and operations, ensures findings are thorough and aligned with business priorities. Stakeholder collaboration is key to producing gap analysis results that actually get acted upon.
Recommended
- Security Consulting for Integrators: Enabling Resilience - Stonos Solutions Blog
- How to Conduct Security Risk Assessment for HIPAA Compliance - Stonos Solutions Blog
- Top 7 security compliance tips for 2026 success - Stonos Solutions Blog
- Blog - Security Insights & Industry News - Stonos Solutions
- Mobile app security best practices every UK business needs
- Web3 development checklist: Secure and optimize your project
Louis Romano
Need Security Consulting?
Our expert team is ready to help you enhance your security posture.
Contact Us Today Download Capability StatementRelated Articles
Enterprise Security Checklist for Healthcare Compliance Success
Explore an actionable enterprise security checklist tailored for healthcare organizations. Follow a step-by-step process to ensure HIPAA compliance and risk management.
Read More7 Key Benefits of Penetration Testing for Healthcare IT
Discover 7 essential benefits of penetration testing for healthcare IT security managers and learn actionable strategies to protect data and ensure compliance.
Read More7 Key Types of Cybersecurity Assessments for Healthcare
Learn about 7 essential types of cybersecurity assessments for healthcare organizations and get actionable tips to boost compliance and security.
Read More