What is a comprehensive security assessment: guide for 2026
What is a comprehensive security assessment: guide for 2026
Cyberattacks on healthcare facilities and government agencies increased by 45% in 2025, forcing organizations to rethink their security strategies. A comprehensive security assessment offers a structured method to identify vulnerabilities, evaluate risks, and build defenses tailored to your organization's unique environment. This guide explains what these assessments involve, which frameworks guide them, and how security managers can apply findings to strengthen cybersecurity posture in regulated sectors where compliance and operational continuity are non-negotiable.
Table of Contents
- Understanding Comprehensive Security Assessments: Definition And Importance
- Key Frameworks And Compliance Standards Guiding Assessments In Regulated Sectors
- Conducting The Comprehensive Security Assessment: Processes And Practical Steps
- Applying Assessment Results To Enhance Cybersecurity Posture And Resilience
- Explore Stonos Solutions' Security Services For Comprehensive Protection
- Frequently Asked Questions
Key takeaways
| Point | Details |
|---|---|
| Assessment scope | Comprehensive security assessments systematically identify threats, vulnerabilities, and risks across your entire infrastructure. |
| Framework guidance | Standards like NIST CSF, FedRAMP, and HIPAA provide structured approaches to meet regulatory requirements and improve security. |
| Practical application | Assessment results inform prioritized mitigation plans with technical controls and procedural improvements. |
| Continuous improvement | Regular reassessment and monitoring ensure your organization adapts to evolving threats and maintains compliance. |
Understanding comprehensive security assessments: definition and importance
A comprehensive security assessment is a systematic evaluation of security risks, threats, and vulnerabilities across your organization's digital and physical infrastructure. Unlike basic vulnerability scans, these assessments examine your entire security ecosystem including networks, applications, data storage, access controls, and operational procedures. They identify weaknesses that attackers could exploit and measure how well your defenses align with industry standards and regulatory requirements.
For healthcare and government organizations, these assessments are critical because cybersecurity threats impact operations daily, disrupting patient care, compromising sensitive data, and threatening public safety. A single breach can expose protected health information (PHI), violate HIPAA regulations, and damage public trust. Government agencies face similar pressures with classified information, citizen data, and critical infrastructure at stake. The financial impact extends beyond immediate remediation costs to include regulatory fines, legal liabilities, and long-term reputational damage.
Regulated sectors face unique challenges that make comprehensive assessments essential:
- Legacy systems that cannot be easily updated or replaced
- Complex compliance requirements across multiple frameworks
- High-value data that attracts sophisticated threat actors
- Interconnected systems where one vulnerability can cascade across networks
- Limited budgets that require strategic prioritization of security investments
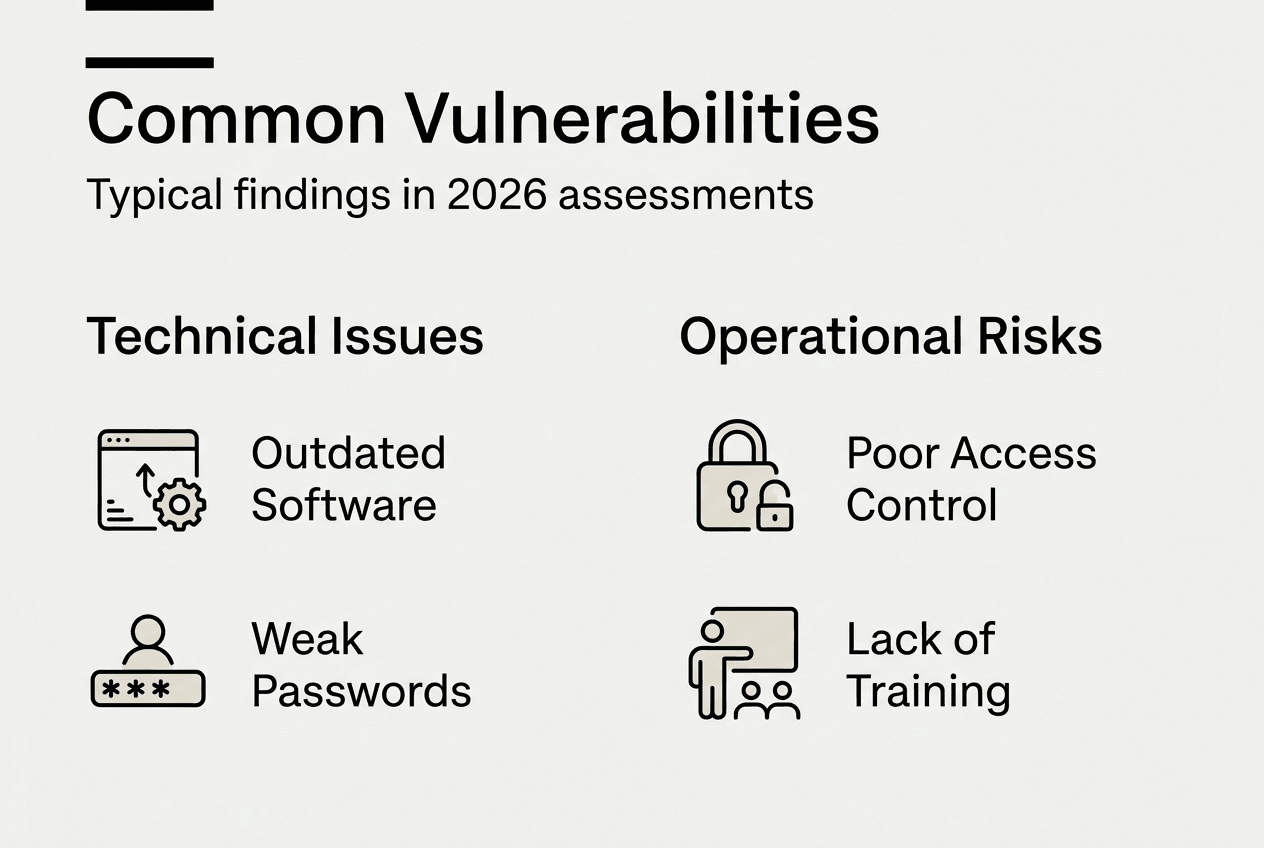
Common vulnerabilities discovered during assessments include outdated software running on critical systems, weak password policies allowing easy credential compromise, unpatched systems exposing known exploits, insufficient network segmentation enabling lateral movement, and inadequate access controls granting excessive privileges. Each vulnerability represents a potential entry point for attackers seeking to steal data, disrupt operations, or establish persistent access for future attacks.
Pro Tip: Start your assessment by mapping all assets that process, store, or transmit sensitive data, then prioritize those with the highest business impact and exposure to external networks.
Understanding how to properly conduct security risk assessments ensures your organization addresses vulnerabilities systematically rather than reactively responding to incidents after they occur.
Key frameworks and compliance standards guiding assessments in regulated sectors
Security frameworks provide structured approaches that guide comprehensive assessments and ensure organizations meet regulatory requirements while building resilient defenses. The NIST Cybersecurity Framework organizes security activities into five core functions: Identify, Protect, Detect, Respond, and Recover. These functions create a complete lifecycle for managing cybersecurity risks. The Identify function establishes asset inventories and risk management processes. Protect implements safeguards for critical infrastructure. Detect develops capabilities to discover security events quickly. Respond defines procedures for containing and mitigating incidents. Recover ensures rapid restoration of services and continuous improvement.
Government agencies and their cloud service providers must comply with FedRAMP requirements, which mandate rigorous security assessments and continuous monitoring. FedRAMP establishes standardized security controls based on NIST guidelines, requiring independent third-party assessments before authorization. Cloud providers must demonstrate compliance across hundreds of controls covering access management, incident response, configuration management, and system monitoring. The authorization process includes detailed documentation, security testing, and ongoing vulnerability scanning to maintain compliance.
Healthcare organizations face HIPAA obligations that require protecting PHI through administrative, physical, and technical safeguards. HIPAA mandates regular risk assessments to identify threats to electronic PHI, implement security measures proportional to identified risks, and document all security decisions and implementations. Required safeguards include access controls limiting data exposure to authorized personnel, encryption protecting data in transit and at rest, audit controls tracking system activity, and integrity controls preventing unauthorized data modification.
| Framework | Primary Purpose | Scope | Key Requirement | | --- | --- | | NIST CSF | Risk management structure | All sectors | Five-function lifecycle approach | | FedRAMP | Cloud security authorization | Government agencies | Continuous monitoring and third-party assessment | | HIPAA | PHI protection | Healthcare providers | Regular risk assessments and documented safeguards | | FISMA | Federal information security | Federal agencies | Annual security assessments and compliance reporting |
These frameworks overlap in many areas, allowing organizations to build unified security programs that satisfy multiple requirements simultaneously. A well-designed assessment program addresses common control families like access management, incident response, and continuous monitoring that appear across all frameworks. This approach reduces duplication while ensuring comprehensive coverage of security domains.
Implementing top risk management strategies for IT security helps organizations align their security programs with these frameworks while addressing sector-specific threats and operational constraints.
Conducting the comprehensive security assessment: processes and practical steps
Executing a thorough security assessment requires systematic methodology that balances technical rigor with practical constraints. The Health Care Coalition Cybersecurity Assessment evaluates cyber resilience and identifies operational gaps, providing a model for structured evaluation. Follow these steps to conduct effective assessments:
- Define scope and objectives by identifying which systems, data, and processes require evaluation based on business criticality and regulatory requirements.
- Inventory assets including hardware, software, data repositories, network infrastructure, and third-party services that connect to your environment.
- Identify threats relevant to your sector such as ransomware targeting healthcare records, nation-state actors pursuing government data, or insider threats from privileged users.
- Discover vulnerabilities through automated scanning tools, manual penetration testing, configuration reviews, and code analysis for custom applications.
- Analyze risks by evaluating the likelihood of threat exploitation and potential impact on operations, data confidentiality, and regulatory compliance.
- Document findings with detailed descriptions of vulnerabilities, affected systems, exploitation scenarios, and recommended remediation actions.
- Present results to stakeholders including executive leadership, IT teams, and compliance officers with clear prioritization and resource requirements.
Automated tools provide efficient vulnerability discovery across large environments. Network scanners identify open ports, outdated services, and misconfigured devices. Web application scanners detect common flaws like SQL injection and cross-site scripting. Configuration management tools verify systems match security baselines. Vulnerability databases provide context about known exploits and available patches.

Manual testing complements automated scans by uncovering logic flaws, business process vulnerabilities, and complex attack chains that tools miss. Penetration testers simulate real attacker techniques to validate whether vulnerabilities are exploitable and assess the effectiveness of security controls. Social engineering tests evaluate whether employees can be manipulated into compromising security through phishing, pretexting, or physical intrusion attempts.
Stakeholder collaboration ensures assessments address real business needs rather than theoretical risks. IT teams provide technical context about system architectures and operational constraints. Security teams contribute threat intelligence and incident response experience. Operations staff explain workflow dependencies and acceptable downtime windows. Compliance officers clarify regulatory requirements and audit expectations. Executive leadership sets risk tolerance and approves resource allocation for remediation.
Pro Tip: Schedule assessments during lower-activity periods to minimize disruption, but ensure testing occurs when systems operate under realistic conditions to identify performance-related vulnerabilities.
Avoid common pitfalls that undermine assessment effectiveness. Scope creep occurs when assessments expand beyond original boundaries without adjusting timelines or resources. Incomplete documentation leaves gaps in understanding vulnerabilities and tracking remediation. Inadequate testing depth misses critical flaws that attackers will discover. Poor communication with stakeholders creates misaligned expectations and resistance to findings.
Professional security consulting for integrators and organizations helps navigate complex assessment requirements while maintaining operational continuity. Specialized penetration testing tools for small businesses enable thorough vulnerability discovery even with limited security staff.
Applying assessment results to enhance cybersecurity posture and resilience
Assessment findings only create value when translated into actionable improvements. Prioritize risks based on two factors: likelihood of exploitation and potential impact on operations. High-likelihood, high-impact risks demand immediate attention regardless of remediation complexity. Low-likelihood, low-impact issues can be accepted or addressed through routine maintenance cycles. Consider factors like public exploit availability, attacker motivation, existing compensating controls, and regulatory requirements when prioritizing.
Develop mitigation plans that combine technical controls with procedural improvements. Technical controls include patching vulnerable software, implementing network segmentation to limit lateral movement, deploying multi-factor authentication for privileged access, encrypting sensitive data at rest and in transit, and configuring security monitoring to detect suspicious activity. Procedural improvements involve updating security policies, training staff on secure practices, establishing incident response procedures, and creating change management processes that prevent new vulnerabilities.
Organizations using NIST CSF report a 20% improvement in detecting and responding to incidents, demonstrating measurable benefits from structured security programs. Track improvements through continuous monitoring and reassessment. Vulnerability management programs track remediation progress and verify fixes are effective. Security metrics measure key performance indicators like mean time to detect incidents, percentage of systems meeting security baselines, and compliance audit findings. Regular reassessments identify new vulnerabilities introduced through system changes, software updates, or evolving threat tactics.
| Vulnerability Type | Associated Risk | Typical Mitigation |
|---|---|---|
| Unpatched systems | Remote code execution | Automated patch management and testing |
| Weak passwords | Credential compromise | Multi-factor authentication and password policies |
| Excessive privileges | Insider threat and lateral movement | Least privilege access and regular reviews |
| Unencrypted data | Data breach and compliance violation | Encryption at rest and in transit |
| Missing monitoring | Delayed incident detection | Security information and event management (SIEM) |
Create remediation roadmaps that sequence improvements logically. Address foundational controls like asset inventory and access management before advanced capabilities like threat hunting. Quick wins that reduce significant risk with minimal effort build momentum and demonstrate value. Long-term initiatives requiring substantial investment need executive sponsorship and phased implementation.
Communicate progress to stakeholders through regular reporting that translates technical findings into business context. Executives need risk reduction metrics and compliance status. IT teams require detailed technical guidance and resource requirements. Compliance officers want evidence of regulatory adherence. Board members seek assurance that cyber risks are managed appropriately relative to organizational risk tolerance.
Advanced risk management strategy guides for 2026 provide frameworks for maintaining security improvements over time. Regular security risk assessments for HIPAA compliance ensure healthcare organizations meet regulatory obligations while adapting to new threats.
Staying informed about cybersecurity trends and threats helps organizations anticipate emerging risks and adjust security strategies proactively rather than reactively responding to incidents.
Explore Stonos Solutions' security services for comprehensive protection
Navigating complex security assessments while maintaining operations requires specialized expertise and proven methodologies. Stonos Solutions delivers comprehensive security services tailored to healthcare and government sector challenges, combining deep technical knowledge with regulatory compliance experience. Our certified professionals conduct thorough assessments that identify vulnerabilities, evaluate risks, and provide actionable remediation guidance aligned with NIST, HIPAA, FedRAMP, and FISMA requirements.

Our penetration testing services simulate real-world attacks to validate your defenses and uncover exploitable weaknesses before threat actors do. We also offer custom development and automation solutions that streamline security operations and enhance monitoring capabilities. Partner with Stonos Solutions to transform assessment findings into measurable security improvements that protect your organization's critical assets and maintain stakeholder trust.
Frequently asked questions
What components are included in a comprehensive security assessment?
Comprehensive security assessments include asset inventory and classification, threat identification relevant to your sector, vulnerability discovery through automated scanning and manual testing, risk evaluation measuring likelihood and impact, and detailed documentation with prioritized remediation recommendations. Assessments also review policies, procedures, and compliance with regulatory frameworks.
How often should organizations conduct security assessments?
Regulated organizations should conduct formal comprehensive assessments annually at minimum, with additional assessments triggered by significant infrastructure changes, new regulatory requirements, or security incidents. Continuous vulnerability scanning and monitoring should occur between formal assessments to identify emerging threats promptly.
What is the difference between vulnerability scanning and comprehensive security assessment?
Vulnerability scanning uses automated tools to identify known security flaws in systems and applications. Comprehensive security assessments include vulnerability scanning plus manual testing, risk analysis, policy review, compliance evaluation, and strategic recommendations that address your organization's unique threat landscape and business requirements.
Who should be involved in the security assessment process?
Effective assessments require participation from IT administrators who manage systems, security teams who understand threats, operations staff who know business processes, compliance officers who track regulatory requirements, and executive leadership who set risk tolerance and approve resources. External assessors provide independent validation and specialized expertise.
How do security assessments support regulatory compliance?
Security assessments demonstrate due diligence by documenting security controls, identifying compliance gaps, and providing evidence for audits. Frameworks like HIPAA and FedRAMP explicitly require regular risk assessments. Assessment findings guide investments in controls that satisfy regulatory requirements while improving overall security posture.
What happens after vulnerabilities are identified in an assessment?
Organizations prioritize vulnerabilities based on risk, develop remediation plans with timelines and resource requirements, implement fixes through patching or configuration changes, verify remediation effectiveness through retesting, and document all actions for compliance and future reference. Continuous monitoring ensures new vulnerabilities are detected and addressed promptly.
Recommended
- Risk management strategy guide 2026: advanced tactics - Stonos Solutions Blog
- How to Conduct Security Risk Assessment for HIPAA Compliance - Stonos Solutions Blog
- Top risk management strategies for IT security 2026 - Stonos Solutions Blog
- Security Consulting for Integrators: Enabling Resilience - Stonos Solutions Blog
- Cybersecurity & Privacy - devPulse
- Cybersecurity Trends & Emerging Threats - Proud Lion Studios
Louis Romano
Need Security Consulting?
Our expert team is ready to help you enhance your security posture.
Contact Us Today Download Capability StatementRelated Articles
Enterprise Security Checklist for Healthcare Compliance Success
Explore an actionable enterprise security checklist tailored for healthcare organizations. Follow a step-by-step process to ensure HIPAA compliance and risk management.
Read MoreRisk management strategy guide 2026: advanced tactics
Master advanced risk management strategies for healthcare, government, and industrial sectors. Build integrated compliance frameworks, reduce incidents, and enhance security posture in 2026.
Read More7 Key Benefits of Penetration Testing for Healthcare IT
Discover 7 essential benefits of penetration testing for healthcare IT security managers and learn actionable strategies to protect data and ensure compliance.
Read More