What is industrial cybersecurity: essential guide for 2026
What is industrial cybersecurity: essential guide for 2026
Industrial control system cyber attacks increased by 87% in 2025, exposing critical vulnerabilities in manufacturing, energy, and utilities that traditional IT security cannot address. Industrial cybersecurity protects operational technology environments where safety and availability trump all other concerns. Misunderstandings about these unique requirements create dangerous gaps in protection. This guide clarifies core concepts, standards, risks, and practical approaches to secure your industrial operations effectively.
Table of Contents
- Definition And Scope Of Industrial Cybersecurity
- Unique Challenges And Risks In Industrial Environments
- Important Standards And Regulations
- Common Attack Methods And Defenses
- Practical Risk Management Methods
- Real-World Industrial Cyber Attack Case Studies
- Common Misconceptions In Industrial Cybersecurity
- Summary And Next Steps For Industrial Cybersecurity Enhancement
- Enhance Your Industrial Cybersecurity With Stonos Solutions
- Frequently Asked Questions
Key takeaways
| Point | Details |
|---|---|
| Industrial cybersecurity protects OT systems distinct from traditional IT environments | OT prioritizes safety and availability over confidentiality, requiring specialized security controls for real-time operations |
| Unique risks include physical safety hazards and legacy system vulnerabilities | Cyber attacks on industrial systems can cause equipment damage, environmental harm, and operational shutdowns |
| Standards like NIST SP 800-82 and ISA/IEC 62443 provide critical frameworks | These guidelines address risk management, system design, and incident response for industrial environments |
| Effective risk management requires cross-team coordination and tailored strategies | IT, OT, and safety teams must collaborate to implement defenses that protect without disrupting critical operations |
| Real-world attacks demonstrate the severe consequences of inadequate industrial security | Case studies reveal how sophisticated threats exploit OT vulnerabilities to cause physical and financial damage |
Definition and scope of industrial cybersecurity
Industrial cybersecurity protects operational technology environments in sectors like manufacturing, energy, water treatment, and transportation. OT systems control physical processes and equipment, fundamentally different from information technology that manages data and communications.
OT environments include SCADA systems that monitor and control distributed infrastructure, DCS that manage continuous industrial processes, and PLCs that automate equipment and machinery. These systems operate in real-time with strict requirements for availability and safety. Standards such as NIST SP 800-82 and ISA/IEC 62443 provide comprehensive frameworks specifically tailored for industrial cybersecurity including risk management, system design, and incident response.
Unlike IT security where confidentiality typically leads priorities, OT security focuses on availability first, integrity second, and confidentiality third. A database breach exposes information, but a compromised control system can shut down production lines, damage equipment, or endanger human life. This priority shift demands specialized security strategies that traditional IT approaches cannot adequately address.
Industrial cybersecurity involves implementing unique controls that accommodate real-time operations and safety requirements. You cannot simply reboot a chemical processing system for updates or block network traffic that controls emergency shutdown systems. Security consulting for integrators helps design protections that balance security with operational continuity.
Key distinctions between IT and OT systems include:
- IT systems manage data and communications; OT systems control physical processes and equipment
- IT tolerates occasional downtime for maintenance; OT requires continuous availability for safety-critical operations
- IT patches systems regularly; OT updates require extensive testing and scheduled outages
- IT protects information confidentiality; OT prevents physical harm and operational disruption
- IT networks change frequently; OT networks remain stable with long-lived equipment
The NIST SP 800-82 guide details these differences and provides risk-based approaches for industrial environments. Understanding this foundation enables you to implement effective security without compromising operational requirements.
Unique challenges and risks in industrial environments
Industrial environments face cybersecurity risks with potentially catastrophic physical consequences. A successful attack on a power grid control system can leave millions without electricity. Compromised safety instrumented systems in chemical plants can cause explosions, toxic releases, or worker injuries. These physical safety risks elevate industrial cybersecurity beyond typical business concerns.
Operational downtime carries massive financial impact in industrial sectors. Manufacturing plants losing production time face costs exceeding $250,000 per hour in some industries. Energy utilities experiencing control system disruptions cannot deliver power to customers, triggering regulatory penalties and revenue loss. Transportation systems suffering cyber incidents strand passengers and disrupt logistics chains.
Legacy OT systems present significant vulnerability challenges. Many industrial control systems run for 15 to 25 years, far exceeding typical IT equipment lifecycles. These systems often lack modern security features like encryption, authentication, or logging. Vendors may no longer support older equipment, eliminating patch availability. You inherit these vulnerabilities when maintaining legacy infrastructure.
Weak authentication and unsafe network configurations compound risks in industrial networks. Default passwords remain unchanged on field devices. Flat network architectures allow lateral movement between systems. Remote access lacks multi-factor authentication. Contractors and vendors connect directly to control networks without proper vetting.
Pro Tip: Regularly update and segment legacy systems to reduce attack surface even when complete replacement remains unfeasible.
Key risk categories in industrial environments include:
- Safety hazards from manipulated control systems causing equipment malfunctions or emergency system failures
- Operational disruption through denial of service attacks, ransomware, or control logic tampering
- Legacy exposure via unpatched vulnerabilities in outdated systems and unsupported equipment
- Insider threats from privileged users with physical access and deep system knowledge
- Supply chain compromise through malicious components, infected firmware updates, or vendor backdoors
Risk management strategies for IT security provide foundations, but industrial environments require additional controls addressing these unique challenges. You must balance security enhancements with operational continuity to protect without disrupting critical processes.
Important standards and regulations
Multiple standards and regulations govern industrial cybersecurity across different sectors. NIST SP 800-82 provides comprehensive guidance for industrial control system security applicable across industries. ISA/IEC 62443 offers a series of standards specifically designed for industrial automation and control system security. NERC CIP regulations mandate cybersecurity requirements for bulk electric system operators.
Standards such as NIST SP 800-82 and ISA/IEC 62443 provide comprehensive frameworks specifically tailored for industrial cybersecurity including risk management, system design, and incident response. Each framework addresses different aspects and applies to specific industrial sectors.
| Standard | Primary Scope | Key Focus Areas | Applicability |
|---|---|---|---|
| NIST SP 800-82 | Industrial control systems across sectors | Risk assessment, network architecture, security controls | Federal agencies and general industry |
| ISA/IEC 62443 | Industrial automation and control systems | Security levels, zones/conduits, product development | Manufacturing, process industries |
| NERC CIP | Bulk electric system | Critical infrastructure protection, asset identification | Electric utilities |
| IEC 61508 | Functional safety systems | Safety integrity levels, lifecycle management | Safety-critical industries |
Common regulatory requirements span these frameworks:
- Risk assessments identifying threats, vulnerabilities, and potential impacts to OT systems
- Network segmentation separating OT from IT networks and creating security zones
- Access controls limiting system access to authorized personnel with defined roles | Incident response plans detailing detection, containment, and recovery procedures
- Security monitoring implementing continuous visibility into OT network activity
- Vendor management ensuring third-party access follows security protocols
Compliance with relevant standards demonstrates due diligence and supports audit readiness. These frameworks provide structured approaches for protecting industrial systems while meeting regulatory obligations. Penetration testing tools help validate control effectiveness and identify gaps before auditors or attackers discover them.
The NIST SP 800-82 guide serves as an excellent starting point for organizations beginning their industrial cybersecurity journey. You should select standards matching your industry sector and regulatory environment, then implement requirements systematically.
Common attack methods and defenses
Cyber attackers targeting industrial control systems exploit specific vulnerabilities unique to OT environments. Legacy system exploitation takes advantage of unpatched vulnerabilities in equipment lacking vendor support or update capabilities. Attackers research known weaknesses in aging control systems and develop exploits specifically targeting industrial protocols.
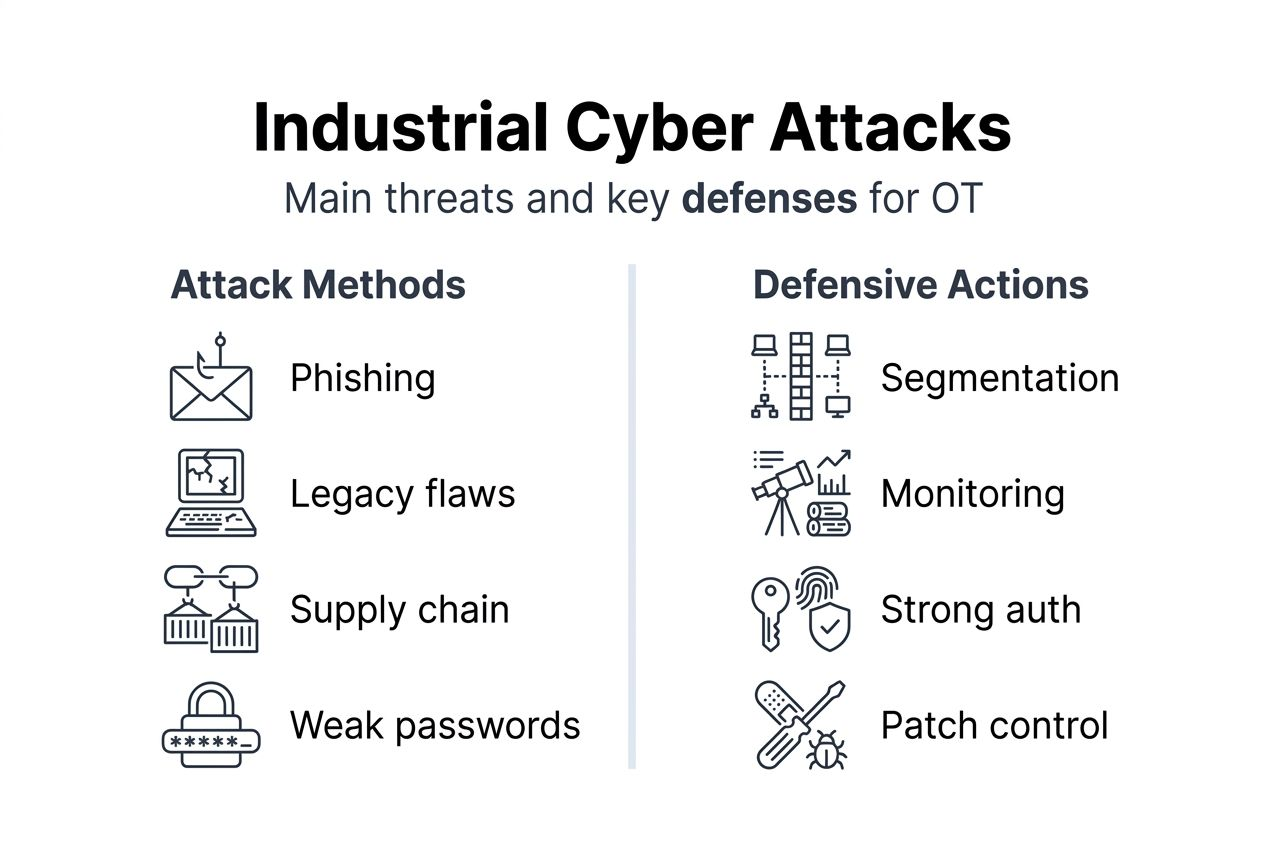
Phishing campaigns target OT personnel to gain initial network access. Engineers and operators receive emails with malicious attachments or links designed to install malware. Once inside the network, attackers move laterally toward control systems. Social engineering exploits trust relationships between operators and vendors.
Supply chain attacks compromise industrial systems before deployment or during maintenance. Malicious actors infiltrate vendor networks to insert backdoors into firmware updates, software packages, or hardware components. These supply chain compromises provide persistent access that bypasses perimeter defenses.
Weak authentication exploits target default credentials, shared passwords, and lack of multi-factor authentication common in OT environments. Attackers use credential stuffing, brute force attacks, or stolen credentials to access control systems, human-machine interfaces, and engineering workstations.
Effective defensive strategies require layered approaches tailored for industrial operations. Network segmentation isolates OT systems from IT networks and external connections using firewalls, data diodes, and demilitarized zones. Segmentation limits attack propagation and contains incidents within defined boundaries.
Strong authentication mechanisms including multi-factor authentication, certificate-based access, and privileged access management reduce unauthorized access risks. You should eliminate default credentials, enforce password policies, and implement role-based access controls appropriate for operational requirements.
Continuous monitoring provides visibility into OT network traffic, system behavior, and potential security events. Specialized OT security monitoring tools detect anomalies, protocol violations, and suspicious activities without disrupting control systems. Security risk assessment methods help identify monitoring priorities.
Patch management for OT requires careful planning to balance security with availability. You should maintain asset inventories, track vulnerabilities, test patches in lab environments, and schedule updates during planned maintenance windows. Virtual patching using network security controls protects systems when direct patching proves impractical.
Pro Tip: Implement layered defense-in-depth architecture customized for OT environments combining network controls, access management, monitoring, and incident response capabilities.
Attack vectors and corresponding defense tactics:
- Legacy vulnerabilities: Asset inventory, virtual patching, network segmentation
- Phishing and social engineering: Security awareness training, email filtering, endpoint protection
- Supply chain compromise: Vendor security requirements, code signing verification, secure boot
- Weak authentication: Multi-factor authentication, privileged access management, credential monitoring
- Network intrusions: Firewalls, intrusion detection systems, security monitoring
Practical risk management methods
Effective industrial cybersecurity risk management requires systematic approaches prioritizing safety, availability, and integrity. You must identify critical assets, assess vulnerabilities, implement proportionate controls, and continuously monitor for threats. This structured process helps allocate resources efficiently while addressing highest risks first.
Follow these key steps for comprehensive risk management:
- Identify and classify OT assets including control systems, network devices, applications, and data flows; document dependencies and criticality to operations and safety
- Conduct impact-focused risk assessments evaluating threats, vulnerabilities, and potential consequences; prioritize risks based on safety impact, operational disruption, and compliance requirements
- Implement segmentation and controls using network zones, access restrictions, and security technologies appropriate for OT environments; balance protection with operational requirements
- Deploy continuous monitoring with OT-aware security tools providing visibility into network traffic, system behavior, and potential incidents; establish baselines and alert thresholds
- Develop coordinated incident response plans defining roles, procedures, and communication protocols across IT, OT, and safety teams; test plans through tabletop exercises
Coordination between IT, OT, and safety teams proves essential for effective response. IT teams understand cybersecurity tools and techniques but may lack OT operational knowledge. OT personnel know systems intimately but may not recognize cyber threats. Safety teams focus on hazard prevention and emergency response. You need all three perspectives working together.
Establish clear communication channels and joint procedures before incidents occur. Define decision authorities for security actions affecting operations. Create escalation paths balancing rapid response with operational safety. Regular cross-team exercises build relationships and clarify roles.
Continuous improvement through monitoring and training maintains security posture over time. Track security metrics including vulnerability counts, patch status, incident frequency, and response times. Conduct regular security assessments identifying new risks. Provide ongoing training keeping personnel current on threats and procedures.
Integrate regulatory requirements into risk processes ensuring compliance activities support operational security. Map controls to applicable standards demonstrating coverage. Document risk decisions and compensating controls for audit evidence. Risk management strategies for IT security provide additional frameworks adaptable to industrial contexts.
Security consulting for integrators helps organizations design and implement risk management programs tailored to their specific operational environments. External expertise accelerates capability development while avoiding common pitfalls. Risk management best practices from other domains offer insights applicable to industrial security.
Real-world industrial cyber attack case studies
Historical industrial cyber attacks demonstrate the severe consequences of inadequate OT security. The Stuxnet worm, discovered in 2010, specifically targeted Iranian nuclear enrichment facilities. This sophisticated attack manipulated PLC code controlling centrifuge speeds, causing physical damage while displaying normal readings to operators. Stuxnet proved that cyber weapons could cause real-world physical destruction in industrial environments.
The 2015 and 2016 attacks on Ukraine's power grid left hundreds of thousands without electricity during winter. Attackers compromised IT networks, moved laterally to OT systems, and remotely operated circuit breakers to disconnect substations. They also corrupted firmware in control equipment, complicating restoration efforts. These incidents showed coordinated attacks could disrupt critical infrastructure at scale.
The 2017 NotPetya ransomware outbreak caused over $10 billion in damages globally, with severe impacts on industrial operations. Manufacturing plants shut down for weeks. Shipping ports could not process containers. Pharmaceutical production halted. Though initially appearing as ransomware, NotPetya actually destroyed data and systems indiscriminately, demonstrating how malware can cascade through interconnected industrial networks.
The Colonial Pipeline ransomware attack in 2021 disrupted fuel supplies across the U.S. East Coast. While the attack initially compromised IT systems, the company proactively shut down pipeline operations fearing OT system compromise. This incident highlighted how IT security failures can force operational shutdowns even without direct OT system impact.
Key takeaways and defenses learned from these cases:
- Network segmentation prevents lateral movement between IT and OT systems
- Monitoring detects suspicious activity before attackers reach critical control systems
- Backup and recovery capabilities enable restoration after destructive attacks
- Incident response plans must address both IT and OT considerations
- Supply chain security prevents compromised components and updates
- Security awareness training helps personnel recognize social engineering attempts
"Industrial cyber attacks have evolved from theoretical concerns to demonstrated threats causing real physical and economic harm. Organizations must treat OT security with the same rigor as safety and environmental protection."
These incidents proved that industrial cybersecurity threats are real, sophisticated, and capable of causing significant harm. You cannot assume air gaps or obscurity protect your systems. Proactive security measures informed by these lessons help prevent similar incidents.
Common misconceptions in industrial cybersecurity
Several widespread misconceptions undermine industrial cybersecurity efforts. Understanding these myths helps you avoid dangerous gaps in protection and implement truly effective security measures.
The belief that traditional IT controls alone can protect OT systems represents a critical misunderstanding. A common misconception is that IT cybersecurity controls are sufficient for protecting industrial environments; however, OT systems require specialized controls due to their real-time, safety-critical nature. Standard IT security tools can disrupt OT operations or fail to address industrial-specific threats. You need OT-aware security solutions designed for operational environments.
Many organizations assume industrial control systems remain isolated from external networks through air gaps. Modern industrial environments feature extensive connectivity for remote monitoring, vendor support, and business system integration. Even systems intended as air-gapped often have unknown connections through wireless devices, contractor laptops, or USB drives. True isolation rarely exists in practice.
The misconception that cybersecurity is primarily a compliance checkbox exercise leads to inadequate protection. While regulatory compliance matters, security requires ongoing risk management beyond minimum requirements. Compliance frameworks provide baselines, not comprehensive security programs. You must address your specific operational risks, not just regulatory checkboxes.
Some believe older OT systems face lower risk because attackers do not know about them. Obscurity provides no real security. Attackers research industrial control systems, develop specialized tools, and share knowledge through underground forums. Legacy systems often have well-documented vulnerabilities that attackers exploit systematically.
Common misconceptions and factual corrections:
- Misconception: IT security tools work for OT systems. Reality: OT requires specialized security solutions respecting operational constraints and industrial protocols.
- Misconception: Air gaps provide sufficient protection. Reality: Modern industrial networks have multiple connectivity points requiring active security controls.
- Misconception: Compliance equals security. Reality: Regulatory requirements establish minimums; comprehensive security requires risk-based programs exceeding baseline standards.
- Misconception: Legacy systems are too old to interest attackers. Reality: Well-documented vulnerabilities in older systems make them attractive targets for exploitation.
- Misconception: Physical security controls prevent cyber attacks. Reality: Cyber and physical security complement each other but neither substitutes for the other.
The IBM OT cybersecurity report details how these misconceptions create exploitable vulnerabilities across industrial sectors. You must recognize and address these misunderstandings to build effective security programs that protect your operations.
Summary and next steps for industrial cybersecurity enhancement
Industrial cybersecurity protects operational technology environments facing unique challenges distinct from traditional IT security. Safety-critical systems, legacy equipment, and real-time operational requirements demand specialized security approaches balancing protection with availability. Standards like NIST SP 800-82 and ISA/IEC 62443 provide frameworks for addressing these unique challenges systematically.
Effective risk management requires identifying critical assets, assessing impact-focused risks, implementing tailored controls, and continuously monitoring threats. Cross-team coordination between IT, OT, and safety personnel ensures security measures support rather than hinder operations. Real-world attacks demonstrate the severe consequences of inadequate industrial cybersecurity, from physical damage to massive operational disruptions.
Immediate actions to enhance your industrial cybersecurity posture:
- Assess OT assets by creating inventories of control systems, network devices, and critical dependencies
- Review compliance requirements mapping applicable standards and regulations to current security controls
- Enhance monitoring by implementing OT-aware security tools providing visibility into industrial network activity
- Train teams through regular security awareness programs and incident response exercises
- Engage specialists for expert assessments, penetration testing, and security architecture review
Risk management strategies and security consulting for integrators provide additional resources supporting your industrial cybersecurity journey. You should prioritize actions addressing your highest risks while building long-term security capabilities.
Enhance your industrial cybersecurity with Stonos Solutions
Protecting your industrial operations requires specialized expertise in OT security challenges, regulatory compliance, and operational continuity. Stonos Solutions delivers tailored security assessments, penetration testing services, and risk management strategies designed specifically for industrial environments. Our team understands the unique requirements of manufacturing, energy, utilities, and critical infrastructure sectors.

We help you identify vulnerabilities in control systems, design secure network architectures, and implement defenses that protect without disrupting operations. Our custom development and automation capabilities address unique industrial security requirements that commercial tools cannot solve. Comprehensive security services support your entire cybersecurity lifecycle from assessment through implementation and ongoing monitoring.
Pro Tip: Partnering with specialized security providers accelerates risk reduction and compliance readiness while leveraging deep OT security expertise.
Frequently asked questions
What is the main difference between IT and industrial cybersecurity?
Industrial cybersecurity protects operational technology focused on safety and availability, unlike IT which mainly prioritizes confidentiality. OT systems control physical processes requiring real-time operation and specialized security controls. Specialized approaches accommodate safety-critical requirements and legacy equipment challenges unique to industrial environments.
Why can't traditional IT security fully protect industrial control systems?
Industrial control systems have unique real-time and safety requirements that traditional IT security tools often disrupt or fail to address. Legacy OT equipment, industrial protocols, and operational constraints demand specialized security solutions designed for continuous availability. Network architectures, update schedules, and risk priorities differ significantly between IT and OT environments.
What are the most common cyber attack methods in industrial environments?
Common attack methods include exploiting unpatched legacy vulnerabilities, phishing targeting OT personnel, weak authentication abuse, and supply chain compromises. Attackers also use industrial protocol manipulation, denial of service attacks, and credential theft to access control systems. These methods take advantage of OT-specific vulnerabilities and operational constraints.
How can organizations comply with industrial cybersecurity regulations effectively?
Compliance requires adopting relevant standards like NIST SP 800-82, ISA/IEC 62443, or NERC CIP alongside risk-based security practices and continuous monitoring. Regular assessments identify gaps between current security posture and regulatory requirements. Cross-team collaboration between IT, OT, and safety personnel enhances both audit readiness and operational security. Risk management strategies for IT security provide frameworks applicable to industrial compliance efforts.
Recommended
- Top risk management strategies for IT security 2026 - Stonos Solutions Blog
- Security Consulting for Integrators: Enabling Resilience - Stonos Solutions Blog
- Top 7 Penetration Testing Tools for Small Business 2026 - Stonos Solutions Blog
- Blog - Security Insights & Industry News - Stonos Solutions
- Business Resilience Strategies for Beginners 2025 Guide | siift
Louis Romano
Need Security Consulting?
Our expert team is ready to help you enhance your security posture.
Contact Us Today Download Capability StatementRelated Articles
Enterprise Security Checklist for Healthcare Compliance Success
Explore an actionable enterprise security checklist tailored for healthcare organizations. Follow a step-by-step process to ensure HIPAA compliance and risk management.
Read More7 Key Types of Cybersecurity Assessments for Healthcare
Learn about 7 essential types of cybersecurity assessments for healthcare organizations and get actionable tips to boost compliance and security.
Read MoreRisk management strategy guide 2026: advanced tactics
Master advanced risk management strategies for healthcare, government, and industrial sectors. Build integrated compliance frameworks, reduce incidents, and enhance security posture in 2026.
Read More