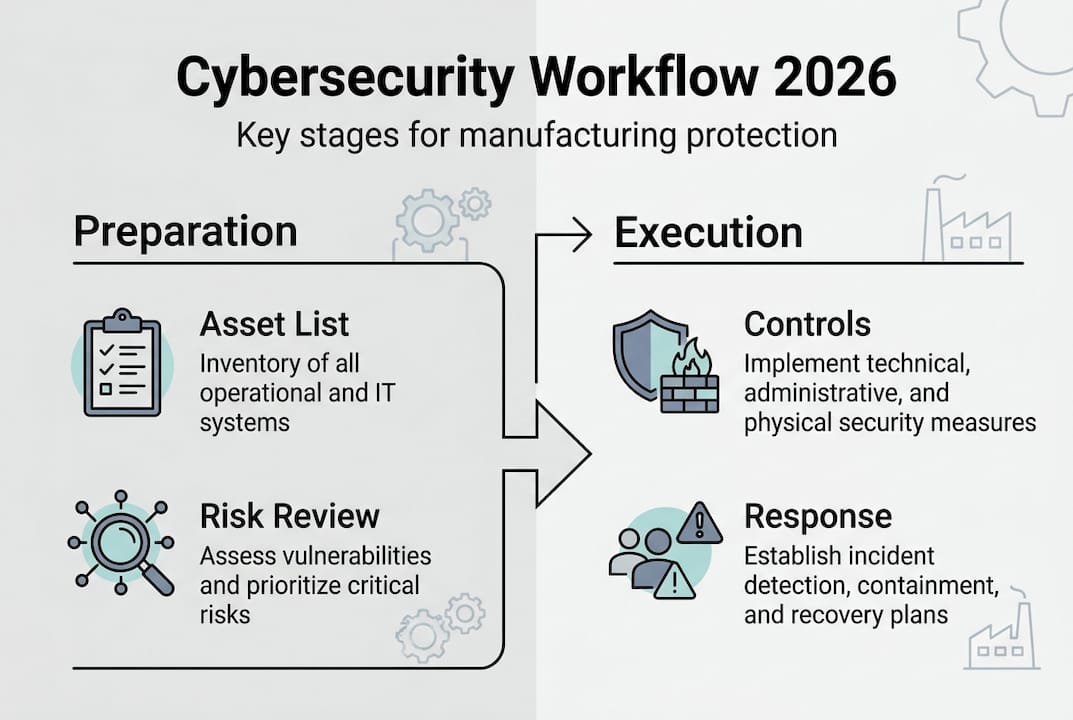
Implement manufacturing cybersecurity workflow in 2026
Implement manufacturing cybersecurity workflow in 2026

Manufacturing facilities face mounting cybersecurity threats that can halt production lines, compromise sensitive data, and violate regulatory requirements. A structured cybersecurity workflow provides the framework you need to protect operational technology systems, maintain compliance, and respond effectively to incidents. This guide walks you through building and implementing a comprehensive manufacturing cybersecurity workflow that strengthens your security posture while supporting business continuity.
Table of Contents
- Key takeaways
- Understanding the problem: cybersecurity risks in manufacturing environments
- Preparation phase: building the foundation with asset inventory and risk assessment
- Execution phase: implementing controls, monitoring, and incident response
- Verification phase: auditing, compliance, and continuous improvement
- Explore Stonos Solutions cybersecurity services
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Structured workflow | A structured cybersecurity workflow provides the framework to protect operational technology systems, maintain compliance, and respond effectively to incidents. |
| Asset inventory foundation | Effective cybersecurity starts with cataloging IT and OT assets to know what to protect and how they connect. |
| Risk assessment vital | Asset risk assessment helps prioritize protections based on criticality and potential impact on operations. |
| Controls and monitoring | Execution focuses on implementing controls, continuous monitoring, and rapid incident handling. |
| Audit and improve | Verification relies on audits and a culture of continuous improvement to strengthen defenses over time. |
Understanding the problem: cybersecurity risks in manufacturing environments
Manufacturing environments face unique cybersecurity risks that threaten both production systems and business operations. The convergence of information technology and operational technology creates attack surfaces that didn't exist when these systems operated in isolation. Cybercriminals increasingly target manufacturing facilities because production downtime translates directly into financial losses and reputational damage.
Your manufacturing environment likely contains a mix of legacy equipment, modern IoT sensors, industrial control systems, and enterprise software. Each component introduces potential vulnerabilities that attackers can exploit. Ransomware attacks can encrypt critical production data and halt operations for days or weeks. Phishing campaigns target employees with access to sensitive systems. Insider threats emerge when disgruntled workers or contractors misuse their authorized access.
Supply chain attacks represent another growing concern. Attackers compromise trusted vendors or software providers to gain access to your network through legitimate channels. This approach bypasses many traditional security controls because the malicious activity appears to come from authorized sources.
Regulatory requirements add another layer of complexity. Manufacturing organizations must comply with industry standards and government regulations that mandate specific security controls and documentation practices. Failure to meet these requirements results in fines, legal liability, and potential loss of contracts.
"The integration of IT and OT systems in manufacturing creates unprecedented security challenges that require specialized workflows and controls to address effectively."
Common cybersecurity threats in manufacturing include:
- Ransomware targeting production control systems
- Phishing attacks aimed at employees with system access
- Unpatched vulnerabilities in legacy equipment
- Unauthorized access through weak authentication
- Data theft of intellectual property and trade secrets
- Supply chain compromises through third party vendors
These risks demand a systematic approach to cybersecurity that goes beyond installing antivirus software or firewalls. You need a comprehensive workflow that identifies assets, assesses risks, implements controls, monitors for threats, responds to incidents, and continuously improves your security posture.
Preparation phase: building the foundation with asset inventory and risk assessment
Effective cybersecurity starts with understanding what you need to protect. Asset inventory provides the foundation for every subsequent security decision. You cannot secure systems you don't know exist or understand how they connect to your network.
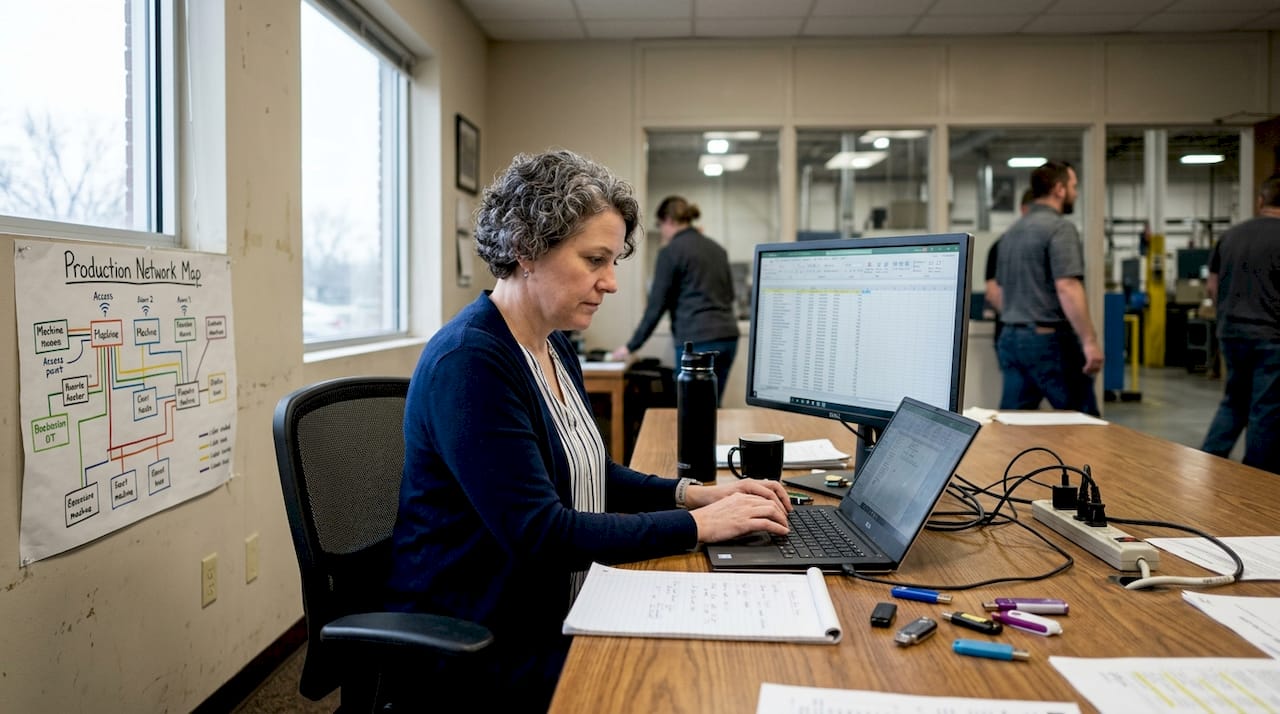
Begin by cataloging all hardware, software, and network components in your manufacturing environment. Include production equipment, control systems, sensors, servers, workstations, mobile devices, and networking infrastructure. Document each asset's location, function, owner, and criticality to operations. Modern asset management tools can automate much of this discovery process, but manual verification ensures accuracy.
Your inventory should capture both IT and OT assets. Many organizations maintain separate inventories for these domains, but integrated visibility is essential for identifying security gaps. A programmable logic controller connected to your corporate network represents both an operational asset and a potential entry point for attackers.
Once you have complete asset visibility, conduct a thorough security risk assessment to identify vulnerabilities and threats. This process evaluates the likelihood and potential impact of various security incidents affecting your manufacturing operations.
- Identify potential threats relevant to your environment
- Analyze vulnerabilities in systems, processes, and controls
- Assess the likelihood of each threat exploiting identified vulnerabilities
- Determine the business impact if security incidents occur
- Calculate risk levels by combining likelihood and impact ratings
- Prioritize risks based on their severity and urgency
Risk management strategies help you evaluate and prioritize cyber risks systematically. Use established frameworks like NIST or ISO 27001 to guide your assessment methodology. These frameworks provide structured approaches that ensure comprehensive coverage of security domains.
Pro Tip: Create a risk register that documents each identified risk, its rating, potential controls, and assigned owner. This living document becomes your roadmap for security improvements and helps track progress over time.
| Asset Type | Common Vulnerabilities | Risk Level | Priority Actions |
|---|---|---|---|
| Legacy PLC systems | Unpatched software, weak authentication | High | Network segmentation, access controls |
| SCADA networks | Unencrypted communications, remote access | Critical | VPN implementation, monitoring |
| IoT sensors | Default credentials, no encryption | Medium | Credential management, firmware updates |
| Employee workstations | Phishing susceptibility, malware | Medium | Security awareness, endpoint protection |
Document your findings in formats that support decision making and compliance requirements. Clear documentation helps justify security investments to leadership and provides evidence of due diligence for auditors and regulators.
Execution phase: implementing controls, monitoring, and incident response
With preparation complete, you can now deploy security controls that protect your manufacturing environment. Effective controls operate at multiple layers to create defense in depth. If attackers bypass one control, others remain in place to detect or stop the intrusion.
Select controls based on your risk assessment priorities. High risk areas demand immediate attention and robust protections. Medium and low risk areas can follow in subsequent phases as resources allow.
- Deploy network segmentation to isolate critical production systems
- Implement strong authentication and access controls
- Install and configure firewalls, intrusion detection systems, and endpoint protection
- Establish secure remote access procedures for vendors and remote workers
- Enable logging and monitoring across all critical systems
- Create backup and recovery procedures for essential data and configurations
Continuous monitoring provides visibility into security events as they occur. You cannot respond to threats you don't detect. Modern security information and event management systems aggregate logs from multiple sources and apply analytics to identify suspicious patterns.
Monitoring approaches vary in sophistication and resource requirements:
- Manual log review requires significant staff time but costs less initially
- Automated monitoring tools process large volumes of data quickly
- Managed security services provide 24/7 coverage without internal staffing
- Hybrid approaches combine internal tools with external expertise
Security consulting for integrators improves resilience by integrating controls and response workflows effectively. Professional guidance helps you select appropriate tools and configure them for your specific environment.
| Monitoring Approach | Pros | Cons | Best For |
|---|---|---|---|
| Manual review | Low cost, full control | Time intensive, limited coverage | Small facilities with basic needs |
| Automated tools | Fast detection, scalable | Requires tuning, false positives | Mid-sized operations with IT staff |
| Managed services | Expert analysis, 24/7 coverage | Higher cost, less control | Large facilities or high risk environments |
Incident response planning ensures you can act quickly when security events occur. Create detailed playbooks that define roles, responsibilities, and procedures for common incident types. Your plan should cover detection, containment, eradication, recovery, and post incident analysis.
Establish an incident response team with representatives from IT, operations, legal, and management. Conduct regular tabletop exercises to practice response procedures and identify gaps. These drills reveal communication breakdowns and unclear responsibilities before real incidents create chaos.
Pro Tip: Integrate custom development automation into your workflow to reduce response times and eliminate manual errors. Automated playbooks can isolate compromised systems, block malicious traffic, and alert responders within seconds of detection.
Document every security incident, even minor events. These records provide valuable data for improving your controls and demonstrate compliance with regulatory requirements. Track metrics like time to detection, time to containment, and time to recovery to measure response effectiveness.
Verification phase: auditing, compliance, and continuous improvement
Regular verification ensures your cybersecurity workflow remains effective as threats evolve and your environment changes. Audits provide independent assessment of your security posture and identify gaps that internal teams might miss.
Schedule comprehensive security audits at least annually, with focused reviews quarterly. External auditors bring fresh perspectives and specialized expertise. Internal audits conducted between external reviews help maintain momentum and catch issues early.
Your audit program should evaluate:
- Completeness and accuracy of asset inventories
- Effectiveness of deployed security controls
- Compliance with applicable regulations and standards
- Incident response capabilities and documentation
- Security awareness and training programs
- Vendor and third party security practices
Security compliance tips are critical for manufacturing sector success in maintaining regulatory alignment. Different industries face different requirements, from NIST standards for government contractors to sector specific regulations for critical infrastructure.
Track compliance status continuously rather than scrambling before audits. Maintain evidence files that document control implementation, testing results, and remediation activities. This proactive approach reduces audit stress and demonstrates your commitment to security.
Use audit findings to drive continuous improvement. Prioritize recommendations based on risk and feasibility. Create remediation plans with clear owners, deadlines, and success criteria. Track progress through regular reviews with leadership.
Pro Tip: Treat security incidents as learning opportunities. Conduct thorough post incident reviews that identify root causes and systemic weaknesses. Share lessons learned across your organization to prevent similar incidents.
Continuous improvement extends beyond fixing problems. Stay informed about emerging threats, new technologies, and evolving best practices. Participate in industry groups and information sharing communities. Benchmark your security program against peers to identify opportunities for enhancement.
Regularly update your risk management strategy as your manufacturing environment evolves. New equipment, processes, or business relationships introduce new risks that require assessment and controls. Schedule risk reassessments whenever significant changes occur.
Measure and report security metrics to leadership. Quantifiable data demonstrates program value and supports resource requests. Track metrics like number of incidents detected, average response time, percentage of systems patched, and compliance audit scores. Present trends over time to show improvement.
Document everything. Comprehensive records support compliance requirements, inform future decisions, and protect your organization legally. Your documentation should tell the story of your security program from initial assessment through ongoing operations.
Explore Stonos Solutions cybersecurity services
Implementing an effective manufacturing cybersecurity workflow requires specialized expertise and proven methodologies. Stonos Solutions delivers comprehensive security services tailored to manufacturing environments, helping you protect operational technology while maintaining production efficiency.

Our penetration testing services identify vulnerabilities before attackers exploit them. We simulate real world attacks against your systems to reveal weaknesses in your defenses. Our team brings deep experience in both IT and OT security, understanding the unique constraints of manufacturing environments.
Streamline your security operations with custom development automation solutions. We build tailored tools that integrate with your existing systems, automate repetitive tasks, and accelerate incident response. Contact us today for a comprehensive security assessment that identifies your highest priority risks and actionable recommendations.
Frequently asked questions
What are the key components of a manufacturing cybersecurity workflow?
The essential components include preparation through asset inventory and risk assessment, execution via security controls and monitoring, and verification through audits and compliance checks. Each phase builds on the previous one to create a comprehensive security program. Continuous improvement ties these phases together, ensuring your workflow adapts to changing threats and business needs.
How often should I conduct cybersecurity risk assessments in manufacturing?
Conduct comprehensive risk assessments annually at minimum, with focused reviews after significant changes to your environment. Major equipment installations, network upgrades, or new business processes all warrant immediate reassessment. Quarterly reviews of your risk register help identify emerging threats and track remediation progress.
What common mistakes should I avoid when implementing this workflow?
Many organizations fail by creating incomplete asset inventories that miss critical systems. Others deploy security controls without proper testing, causing production disruptions. Neglecting incident response drills leaves teams unprepared when real attacks occur. Avoid treating cybersecurity as a one time project rather than an ongoing program that requires sustained attention and resources.
How can automation improve manufacturing cybersecurity workflows?
Automation accelerates threat detection by analyzing security events faster than human analysts can. Automated response playbooks contain incidents within seconds, minimizing damage and downtime. Automation in cybersecurity workflows reduces human error in repetitive tasks like log analysis and patch deployment. This consistency improves your overall security posture while freeing staff to focus on strategic initiatives that require human judgment.
Recommended
- Role of security in manufacturing: protect assets now - Stonos Solutions Blog
- Top 7 security compliance tips for 2026 success - Stonos Solutions Blog
- Top risk management strategies for IT security 2026 - Stonos Solutions Blog
- Custom Development & Automation - Stonos Solutions
- AI Security Implementation: Protect Your Systems
Louis Romano
Need Security Consulting?
Our expert team is ready to help you enhance your security posture.
Contact Us Today Download Capability StatementRelated Articles
Security gap analysis: steps, benefits, and best practices
Learn how to conduct a security gap analysis to identify hidden risks, close compliance gaps, and build a stronger security posture in regulated industries.
Read MoreEnterprise Security Checklist for Healthcare Compliance Success
Explore an actionable enterprise security checklist tailored for healthcare organizations. Follow a step-by-step process to ensure HIPAA compliance and risk management.
Read More7 Key Types of Cybersecurity Assessments for Healthcare
Learn about 7 essential types of cybersecurity assessments for healthcare organizations and get actionable tips to boost compliance and security.
Read More