Secure network design: frameworks and steps for compliance
Secure network design: frameworks and steps for compliance

TL;DR:
- Proper network segmentation prevents lateral movement and protects sensitive data in regulated industries.
- Frameworks like NIST, CIS Controls, and CISA guide practical network security design.
- Asset inventory, segmentation, strict access, monitoring, and continuous testing are essential for compliance.
Poor network segmentation in regulated industries is not a minor oversight. A single misconfigured boundary can expose protected health information, trigger PCI-DSS penalties, or invite lateral movement that shuts down critical operations. The core mechanics of secure design include segmentation, least privilege access, zero trust principles, defense-in-depth, and continuous monitoring. For IT security managers and compliance officers, these are not abstract ideals. They are the structural requirements that determine whether your organization survives an audit or a breach. This guide walks through the principles, frameworks, and actionable steps that regulated industries need to build networks that hold up under real-world pressure.
Table of Contents
- Critical principles in secure network design
- Mapping frameworks to design: NIST, CIS, CISA, and sector regulations
- Step-by-step network hardening for regulated environments
- Addressing edge cases: OT security, hybrid cloud, GenAI, and wireless
- A new lens on network security: Policy, integration, and constant verification
- Advance your network security with expert support
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Start with asset inventory | Identifying and classifying systems is the very first step toward secure compliant network design. |
| Use Zero Trust principles | Zero Trust, microsegmentation, and least privilege policies are essential for modern network security and regulatory demands. |
| Align with compliance frameworks | Map your network security controls to NIST, CIS, PCI-DSS, or HIPAA requirements for defensible architectures. |
| Design for edge cases | Include OT, hybrid cloud, and wireless/guest controls as standard to close critical security gaps. |
| Verify and audit regularly | Continuous monitoring and annual auditing ensure secure network design stands up to evolving threats and regulations. |
Critical principles in secure network design
Secure network design is not a single control. It is a layered architecture where each principle reinforces the others. For regulated organizations, getting this right means the difference between a defensible posture and a compliance gap that auditors will flag immediately.
Network segmentation is the practice of dividing a network into isolated zones so that a compromise in one area cannot freely spread to others. In regulated environments, this means separating systems that handle sensitive data, such as electronic health records or cardholder data, from general corporate traffic. Virtual networks (VNets) and network security groups (NSGs) are common tools for enforcing these boundaries in cloud environments.
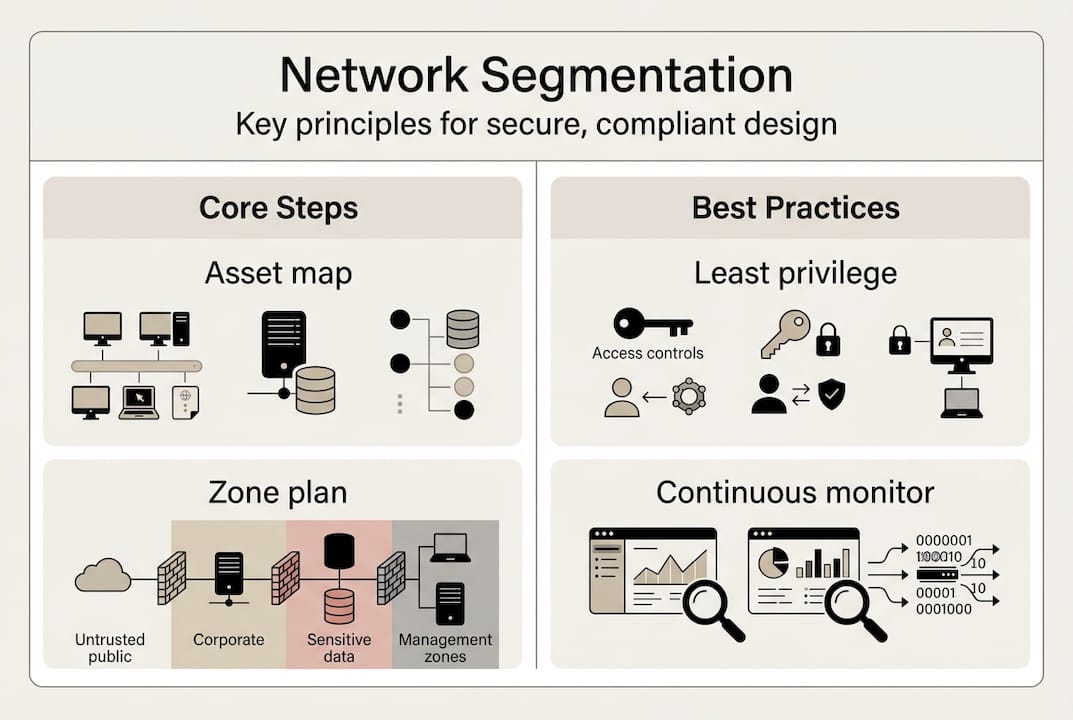
Least privilege access means every user, device, and service gets only the access it needs and nothing more. Applied to network design, this translates to default-deny rules at every boundary. If a connection is not explicitly permitted, it is blocked.
Zero Trust Architecture (ZTA) extends least privilege by assuming that no device or user is inherently trustworthy, even inside the perimeter. Identity verification and microsegmentation are the two pillars of ZTA in network design. Every session is authenticated, and traffic between workloads is restricted based on policy.
Continuous monitoring closes the loop. Without real-time visibility into traffic patterns, policy violations, and anomalies, you cannot verify that your design is working as intended. This is a direct requirement under frameworks like HIPAA and NIST CSF (Cybersecurity Framework).
As NIST SP 1800-35 confirms, these mechanics form the foundation of any modern defensible architecture. CIS Control 12.2 specifically addresses segmentation, least privilege, and availability as core network requirements.
| Principle | Compliance benefit | Example control |
|---|---|---|
| Segmentation | Limits breach scope | VNets, VLANs, NSGs |
| Least privilege | Reduces attack surface | Default-deny ACLs |
| Zero Trust | Continuous verification | Identity-aware proxy |
| Monitoring | Audit trail, detection | SIEM, flow logs |
Organizations in industrial sectors can find additional context on how these principles apply operationally in security in manufacturing environments.
- Segment by data sensitivity, not just by function
- Enforce default-deny at every network boundary
- Authenticate every session, including internal traffic
- Log all traffic and review alerts on a defined schedule
Pro Tip: Start with your highest-risk data zone. Segment it first, verify controls, then expand outward. Trying to segment everything at once often results in broken dependencies and rollback.
Mapping frameworks to design: NIST, CIS, CISA, and sector regulations
With core principles in mind, you need to build your design on the right foundations. Here's how frameworks directly inform practical network decisions.
The primary frameworks shaping secure network design in regulated industries are NIST SP 800-207 (Zero Trust Architecture), CIS Controls v8, and CISA Cross-Sector Cybersecurity Performance Goals (CPGs). Each one provides a different lens, but they are designed to complement each other.
NIST SP 800-207 defines ZTA as a set of principles where no implicit trust is granted based on network location. It requires a policy engine, policy administrator, and policy enforcement points throughout the network. For compliance officers, this framework maps directly to HIPAA's access control requirements and PCI-DSS network isolation mandates.

CIS Controls v8.1 organizes 18 controls across IG1 to IG3 implementation groups, where IG1 represents the minimum baseline for any organization. Control 12 covers network infrastructure management and is the most directly relevant to design decisions.
CISA CPGs provide cross-sector benchmarks for critical infrastructure operators. The CISA CPG Report 2.0 organizes goals around Govern, Identify, Protect, Detect, and Respond categories, making it easy to map against existing frameworks like SOC 2 and PCI-DSS 4.0.
As NIST SP 1800-35 documents, methodologies from these established frameworks provide 19 real-world ZTA implementation examples across different sector types.
| Framework | Key design element | Sector relevance |
|---|---|---|
| NIST SP 800-207 | Policy engine, microsegmentation | Federal, healthcare |
| CIS Controls v8.1 | IG1 baseline, network controls | All regulated sectors |
| CISA CPGs | Cross-sector performance goals | Critical infrastructure |
| PCI-DSS 4.0 | Cardholder data isolation | Financial, retail |
| HIPAA | Access control, audit logs | Healthcare |
Here is a practical sequence for baseline implementation:
- Complete an asset inventory covering all devices, services, and data flows
- Apply IG1 controls from CIS v8.1 as your minimum baseline
- Segment networks based on data classification and regulatory scope
- Enforce multi-factor authentication (MFA) at all network access points
- Deploy policy enforcement points aligned with NIST ZTA principles
- Enable logging and monitoring across all segmented zones
For a broader view of how these frameworks translate into organizational practice, the security compliance tips resource covers practical alignment strategies worth reviewing alongside this guide.
Step-by-step network hardening for regulated environments
Next, let's move from principles and frameworks to an actionable step-by-step plan tailored for compliance-heavy industries.
Network hardening is not a one-time project. It is a phased process that requires planning, testing, and ongoing verification. The following steps apply across healthcare, financial services, government, and industrial sectors.
- Inventory all assets. Document every device, workload, and data flow. You cannot segment what you have not mapped. Include cloud resources, OT (operational technology) devices, and remote endpoints.
- Classify and segment. Group assets by data sensitivity and regulatory scope. Place systems handling protected data in isolated zones with strict boundary controls.
- Restrict access. Apply default-deny rules at every boundary. Use identity-aware controls so that only verified users and services can cross zone boundaries.
- Enable monitoring. Deploy flow logging, intrusion detection, and SIEM (Security Information and Event Management) integration across all segments. Ensure logs are retained per regulatory requirements.
- Test controls. Run penetration tests and configuration audits to verify that segmentation is working as designed. Validate that no unintended paths exist between zones.
- Review and improve. Schedule annual reviews and trigger reviews after any major network change or regulatory update.
For hybrid and multi-cloud environments, apply the same segmentation logic across cloud-native boundaries. Use cloud provider tools to enforce policies consistently. OT environments require additional care because legacy protocols often cannot support modern authentication. Isolate OT networks from IT networks at the hardware level where possible.
As ZTA alignment for regulated industries confirms, aligning with NIST CSF, PCI-DSS, and HIPAA through identity verification, microsegmentation, and monitoring is the most effective path to compliance-ready network design. The CISA CPG Report 2.0 reinforces this with its Govern, Identify, Protect, Detect, and Respond structure.
Warning: Skipping the asset inventory phase is the most common cause of segmentation failures. Incomplete maps lead to broken application dependencies and emergency rollbacks that delay compliance timelines by months.
Pro Tip: Use your penetration test results as input for your next segmentation review. Testers often find lateral movement paths that internal teams miss because they are too close to the architecture.
For organizations building or refining their overall security posture, risk management strategies provide a useful framework for prioritizing hardening efforts alongside other security investments. The NIST ZTA reference remains the authoritative source for implementation guidance.
Addressing edge cases: OT security, hybrid cloud, GenAI, and wireless
Some environments demand extra scrutiny and tailored controls due to unique risks and compliance needs.
Flat networks in OT environments are one of the most dangerous configurations in regulated industries. When IT and OT systems share the same network without segmentation, a compromise on the corporate side can reach industrial control systems directly. Third-party breaches from OT issues account for up to 30% of incidents in critical infrastructure sectors, and egress filtering with default-deny enforcement is one of the most effective mitigations.
OT-specific considerations:
- Physically or logically separate IT and OT networks at all times
- Use data diodes or unidirectional gateways where bidirectional communication is not required
- Apply strict egress rules to prevent OT devices from initiating outbound connections
- Inventory all OT assets separately and apply firmware patching schedules
Hybrid and multi-cloud gaps are another common blind spot. Organizations often assume that cloud provider security covers their segmentation needs. It does not. You are responsible for configuring security groups, access policies, and traffic inspection within your cloud tenancy. Inconsistent policy enforcement across cloud and on-premises environments creates gaps that attackers exploit.
Wireless and guest network isolation is a compliance requirement under PCI-DSS and a best practice under HIPAA. Guest networks must never share a segment with systems that process regulated data. Use separate SSIDs, VLANs, and firewall rules to enforce this boundary.
GenAI and data leakage represent an emerging risk. Employees using AI tools may inadvertently submit regulated data to external services. Egress filtering and data loss prevention (DLP) policies at the network layer can intercept these transfers before they become a breach.
- Enforce egress filtering on all segments, not just ingress
- Apply DLP policies at the network boundary for regulated data types
- Monitor DNS queries for connections to unauthorized AI or cloud services
- Isolate guest and wireless traffic from all regulated workloads
For organizations supporting system integrators, security consulting for integrators covers how these edge case controls translate into practical project requirements.
A new lens on network security: Policy, integration, and constant verification
Most organizations treat the firewall as the finish line. Once traffic is blocked at the perimeter, the assumption is that the network is secure. This thinking is not just outdated. It is actively dangerous in environments where lateral movement, insider threats, and supply chain compromises are the primary attack vectors.
The real foundation of a secure network is enforceable policy, not perimeter hardware. As Valydex's network security guidance makes clear, mapping dependencies before segmenting and integrating network controls with EDR (Endpoint Detection and Response) and SIEM tools is what separates organizations that detect breaches quickly from those that discover them months later.
Most organizations skip the dependency mapping step because it is time-consuming. That shortcut creates segmentation that breaks production applications and forces rollbacks. The result is a network that looks segmented on paper but has exception rules that effectively defeat the controls.
The other missing piece is integration. Network segmentation without EDR and SIEM integration means you have boundaries but no visibility into what crosses them. Real-time policy enforcement, tied to threat intelligence and endpoint telemetry, is what makes segmentation operationally effective rather than just compliant on paper. Organizations focused on security for manufacturing and other high-risk sectors understand this distinction because the consequences of a missed detection are immediate and physical.
Advance your network security with expert support
With compliance-critical networks, expert guidance can mean the difference between passing an audit and suffering a costly breach.

Stonos Solutions brings certified expertise in secure network design, regulatory compliance, and security assessment to organizations across healthcare, government, industrial, and enterprise sectors. Whether you are building a new architecture or closing gaps in an existing one, our team can support your design and specifications process from baseline planning through full documentation. We also offer penetration testing services to validate that your segmentation and access controls hold up under real attack conditions. For organizations preparing for audits or regulatory reviews, our full range of security services covers gap assessments, compliance mapping, and ongoing advisory support.
Frequently asked questions
What is the most important first step in secure network design for regulated industries?
The first step is a thorough asset inventory followed by segmentation of critical systems. CISA CPG 2.0 prioritizes this sequence as the foundation for ZTA implementation in regulated environments.
How can Zero Trust help with PCI-DSS or HIPAA compliance?
Zero Trust enforces strict identity verification, microsegmentation, and continuous monitoring, which directly satisfies PCI-DSS and HIPAA access control and audit requirements.
What are common mistakes in network segmentation?
The two most common mistakes are skipping dependency mapping before segmenting and relying solely on perimeter firewalls. Mapping dependencies first and integrating EDR and SIEM tools prevents both errors.
How often should network security be audited in regulated sectors?
Audits should occur at least annually and after any significant network or regulatory change. Microsoft's security maturity model recommends phased rollouts with annual audit cycles as part of a structured maturity program.
Recommended
- Top 7 security compliance tips for 2026 success - Stonos Solutions Blog
- Regulatory Compliance Explained: Build Stronger Security - Stonos Solutions Blog
- Security Consulting for Integrators: Enabling Resilience - Stonos Solutions Blog
- Role of security in manufacturing: protect assets now - Stonos Solutions Blog
- Website security essentials: 5 steps every SMB needs - Ibrandmedia
- Simple Tips for Website Security | Big Eye Deers Blog
Louis Romano
Need Security Consulting?
Our expert team is ready to help you enhance your security posture.
Contact Us Today Download Capability StatementRelated Articles
Enterprise Security Checklist for Healthcare Compliance Success
Explore an actionable enterprise security checklist tailored for healthcare organizations. Follow a step-by-step process to ensure HIPAA compliance and risk management.
Read MoreSecurity gap analysis: steps, benefits, and best practices
Learn how to conduct a security gap analysis to identify hidden risks, close compliance gaps, and build a stronger security posture in regulated industries.
Read More7 Key Benefits of Penetration Testing for Healthcare IT
Discover 7 essential benefits of penetration testing for healthcare IT security managers and learn actionable strategies to protect data and ensure compliance.
Read More