Why assess industrial security risks for compliance
Why assess industrial security risks for compliance

Many organizations assume traditional IT risk methods protect industrial environments, but FDA medical device manufacturers improve OT security because operational technology demands specialized assessment frameworks that prioritize exploitability over probability. Industrial security risks intersect with physical safety, production continuity, and strict regulatory compliance in ways conventional cybersecurity approaches cannot address. Healthcare facilities, manufacturing plants, and other regulated sectors face unique vulnerabilities where a breach could halt operations, endanger lives, or trigger severe penalties. Understanding how to assess these risks properly ensures your organization meets compliance mandates while protecting critical assets against evolving threats.
Table of Contents
- Key takeaways
- Understanding the critical need to assess industrial security risks
- Core methodology: IEC 62443 zone and conduit model for effective risk assessment
- Navigating challenges: safety limits, physical constraints, and cyber resilience in industrial settings
- Applying industrial security risk assessments for compliance and operational resilience
- Explore Stonos Solutions' industrial security expertise
- FAQ
Key Takeaways
| Point | Details |
|---|---|
| Exploitability focus | Industrial risk assessments prioritize exploitability over probability due to unpredictable actors in OT environments. |
| IEC 62443 zoning | The core methodology structures assessments around zones and conduits to map access and control paths in industrial control systems. |
| Regulatory drivers | FDA premarket cybersecurity risk management, HIPAA risk analysis, NIST Cybersecurity Framework, and state breach rules require evidence of protective measures across the lifecycle. |
| Safety cyber integration | Security programs must integrate safety and cybersecurity processes to protect people, assets, and continuous operations. |
| Consequence based risk | The assessment prioritizes consequences over likelihood because attackers may exploit any vulnerability given enough time. |
Understanding the critical need to assess industrial security risks
Regulated industries face fundamentally different security challenges than typical IT environments. Healthcare organizations and manufacturing facilities operate complex operational technology systems where security compliance tips for 2026 must address both digital vulnerabilities and physical safety requirements. The FDA and other regulatory bodies mandate risk assessments that focus on exploitability rather than probability because threat actors in industrial contexts operate unpredictably, making traditional likelihood calculations unreliable.
Industrial security risks impact three critical dimensions simultaneously: safety, production continuity, and regulatory compliance. A compromised programmable logic controller could trigger equipment failures that endanger workers, halt manufacturing lines costing millions per hour, and violate HIPAA or FDA requirements in a single incident. Traditional IT risk management methods evaluate data confidentiality and system availability but rarely account for physical consequences or safety-critical operations that define industrial environments.
The distinction matters because conventional cybersecurity frameworks assume you can patch systems quickly, isolate compromised assets, and restore from backups without catastrophic consequences. Industrial control systems often run legacy equipment that cannot be patched without extended downtime, operate in continuous processes where isolation means production loss, and control physical equipment where restoration failures could cause explosions or toxic releases. Your risk assessment methodology must reflect these realities.
Key compliance drivers reshape how you evaluate industrial security risks:
- FDA premarket guidance requires medical device manufacturers to demonstrate cybersecurity risk management throughout product lifecycles
- HIPAA Security Rule mandates risk analysis for all electronic protected health information systems, including medical devices and building automation
- NIST Cybersecurity Framework emphasizes identifying and protecting critical infrastructure assets before implementing detection and response
- State regulations increasingly require breach notification for operational technology incidents affecting critical services
"Assessing industrial security risks ensures regulatory compliance in healthcare and manufacturing, where specialized cybersecurity risk assessments focus on exploitability due to unpredictable threats. Traditional probability models fail when adversaries can choose timing and methods unpredictably."
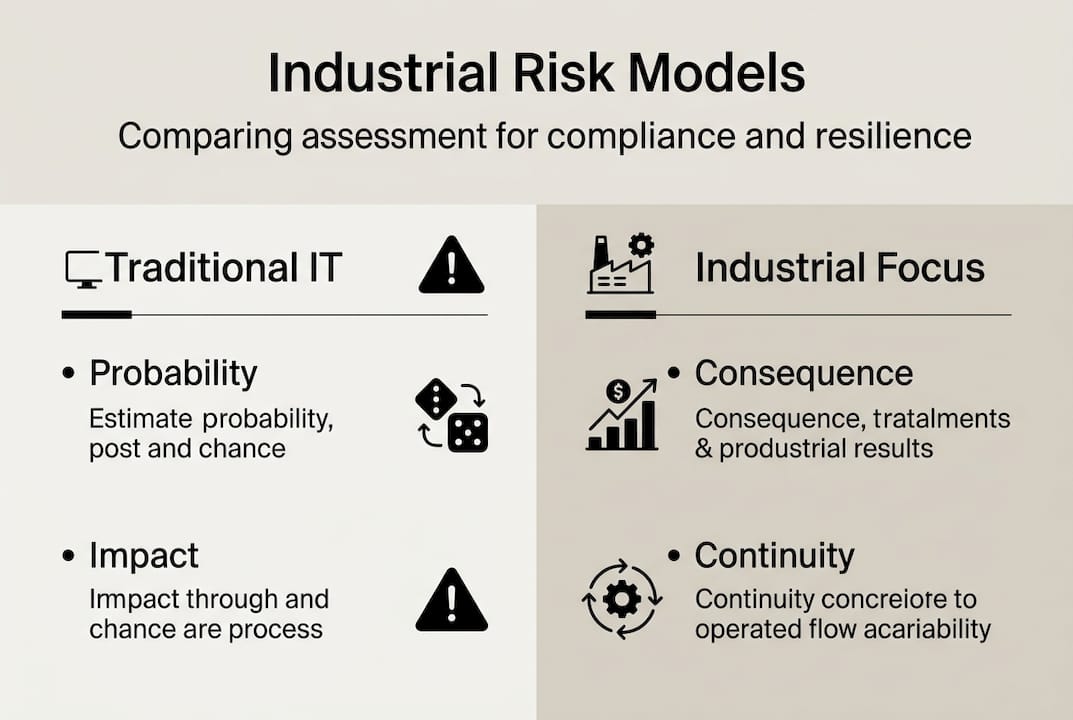
This regulatory landscape forces security managers to adopt assessment frameworks that quantify consequences rather than likelihood. When a motivated attacker can exploit any vulnerability given enough time and resources, your risk calculation must prioritize what happens when a breach occurs, not whether one might happen. The shift from probability-based to consequence-based evaluation fundamentally changes how you identify critical assets, allocate security resources, and demonstrate compliance to auditors.
Core methodology: IEC 62443 zone and conduit model for effective risk assessment
The IEC 62443-3-2 standard provides the foundational methodology for industrial security risk assessment through its Zone and Conduit Risk (ZCR) model. This framework begins by defining your System under Consideration, which encompasses all assets, networks, and processes requiring protection within a specific operational boundary. You establish clear scope boundaries that separate your industrial control system from enterprise IT networks, external vendor connections, and physical plant infrastructure.
The ZCR methodology structures risk evaluation through five systematic steps:
- Partition your System under Consideration into security zones based on similar security requirements, asset criticality, and operational functions
- Identify conduits representing all communication paths between zones, including network connections, removable media, and human interfaces
- Document threats applicable to each zone and conduit using standardized threat catalogs that cover both cyber and physical attack vectors
- Estimate risk levels by evaluating potential consequences and exploitability for each identified threat
- Select appropriate countermeasures from security level target definitions that reduce risk to acceptable thresholds
This structured approach differs from traditional risk methods by emphasizing boundaries and flows rather than individual asset vulnerabilities. You group similar assets into zones sharing security requirements, then focus protection efforts on controlling what crosses zone boundaries through conduits. The model recognizes that industrial environments cannot implement uniform security controls across all systems due to operational constraints, safety requirements, and legacy equipment limitations.
| Assessment aspect | IEC 62443 ZCR approach | Traditional IT risk method |
|---|---|---|
| Primary focus | Zone boundaries and conduits | Individual asset vulnerabilities |
| Risk calculation | Consequence and exploitability | Probability and impact |
| Scope definition | System under Consideration with operational context | Network segments and data classifications |
| Countermeasure selection | Security level targets by zone | Uniform controls across environment |
| Integration requirements | Safety standards and operational needs | Business continuity and data protection |
Implementing the ZCR methodology requires understanding that zones represent logical groupings, not necessarily physical network segments. A single manufacturing cell might contain multiple zones if some controllers handle safety-critical functions while others manage quality monitoring. Similarly, a conduit between your supervisory control and data acquisition system and enterprise resource planning network represents a critical trust boundary requiring strong access controls, even if both systems physically reside in the same data center.
Pro Tip: Leverage tool-supported risk assessment platforms that automate threat catalog application and countermeasure mapping to IEC 62443 security levels. Manual ZCR assessments become impractical for complex industrial environments with hundreds of zones and conduits, but specialized software can maintain consistency while reducing practitioner burden. Choose tools that integrate with your existing asset management systems to avoid duplicate data entry and ensure assessment accuracy.
The framework's power lies in its scalability and adaptability. Small facilities might define five to ten zones covering basic operational areas, while large manufacturing complexes could identify hundreds of zones across multiple production lines, utilities, and support systems. You tailor the granularity to match your operational complexity, regulatory requirements, and available security resources. This flexibility makes IEC 62443 applicable across diverse regulated industries from pharmaceutical manufacturing to medical device production.
Navigating challenges: safety limits, physical constraints, and cyber resilience in industrial settings
Certain industrial components operate under constraints that make conventional cybersecurity measures impossible to implement. Level 0 sensors cannot implement IEC 62443-4-2 requirements or Cyber Resilience Act provisions because intrinsic safety certifications limit their electrical characteristics to prevent ignition in hazardous atmospheres. These sensors in explosive environments must restrict energy levels below ignition thresholds, leaving insufficient power for cryptographic processors, authentication protocols, or firmware update mechanisms.

Intrinsic safety standards like IEC 60079 govern equipment used in zones containing flammable gases, vapors, or combustible dusts. A temperature sensor monitoring a chemical reactor or pressure transmitter in a grain elevator cannot incorporate the processing power needed for secure boot, encrypted communications, or digital signatures without exceeding safe energy limits. Traditional cybersecurity controls assume devices have computational resources for implementing protection mechanisms, but physics-based safety requirements trump digital security in these contexts.
Your risk assessment must account for these edge cases through alternative monitoring and protection strategies. Instead of securing the sensors themselves, you focus on detecting anomalies in their physical behavior and protecting the communication paths they use. This approach recognizes that you cannot eliminate vulnerabilities in intrinsically safe devices, but you can detect and respond to exploitation attempts through complementary controls.
Alternative monitoring techniques for constrained industrial components include:
- Physics-based anomaly detection comparing sensor readings against known physical relationships and process constraints
- Communication protocol analysis identifying deviations from expected message patterns, timing, and sequencing
- Environmental correlation checking sensor outputs against independent measurements from different technology types
- Statistical process control detecting gradual drift or sudden changes inconsistent with normal operations
- Redundant sensing using diverse sensor technologies to cross-validate critical measurements
These monitoring approaches leverage the physical laws governing industrial processes to detect manipulation attempts. A spoofed temperature reading that violates thermodynamic relationships with pressure and flow measurements reveals potential compromise even when you cannot authenticate the sensor itself. You build resilience through diversity and correlation rather than hardening individual components.
Integrating safety standards ISO 14971 and IEC 61508 with cybersecurity risk assessment creates comprehensive protection frameworks. ISO 14971 provides medical device risk management processes focusing on patient safety, while IEC 61508 defines functional safety requirements for electrical, electronic, and programmable systems. Both standards emphasize hazard analysis, risk evaluation, and risk control measures that complement cybersecurity objectives. When you align these frameworks, your assessment identifies scenarios where cyber attacks could trigger safety hazards, and your countermeasures address both digital and physical risks simultaneously.
Pro Tip: Establish joint review processes where safety engineers and cybersecurity professionals evaluate risk scenarios together. Safety teams understand physical hazards and protection mechanisms, while security teams recognize attack vectors and exploitation techniques. Combined expertise identifies risks neither discipline would catch independently, such as cyber attacks that disable safety instrumented systems or manipulate process parameters to create hazardous conditions. Document these integrated assessments to demonstrate regulatory compliance with both safety and security requirements.
The challenge extends beyond sensors to actuators, safety controllers, and emergency shutdown systems operating under similar constraints. Your security consulting for integrators must address how to protect these components through network segmentation, protocol filtering, and behavioral monitoring rather than endpoint hardening. You create security architectures that assume Level 0 and Level 1 devices remain vulnerable while preventing attackers from exploiting those vulnerabilities to cause harm.
Applying industrial security risk assessments for compliance and operational resilience
Traditional IT risk assessment calculates probability multiplied by impact to prioritize vulnerabilities, but operational technology security requires consequence-based evaluation because motivated attackers make probability estimates meaningless. When nation-state actors or sophisticated criminals target industrial facilities, they invest time and resources to overcome defenses regardless of initial difficulty. Your risk calculation must focus on what happens when they succeed, not how likely success appears based on current vulnerability scans.
The Purdue Model 2.0 framework enables converged IT/OT segmentation that supports comprehensive risk assessment across enterprise and operational technology domains. This updated architecture recognizes that strict separation between business systems and industrial controls creates operational inefficiencies while failing to address modern threats. Instead, you implement controlled integration points with robust monitoring, allowing necessary data flows while maintaining visibility and protection. The model defines security zones from field devices through supervisory control up to enterprise resource planning, with clearly specified trust boundaries and access controls at each level.
Implementing industrial risk assessments for regulatory compliance requires systematic execution:
- Define your System under Consideration boundaries encompassing all assets, networks, and processes requiring protection under applicable regulations
- Identify applicable compliance requirements from FDA, HIPAA, NIST, or industry-specific standards that mandate risk assessment activities
- Partition systems into security zones based on criticality, safety requirements, and operational functions using IEC 62443 methodology
- Document threats using standardized catalogs covering cyber attacks, physical intrusion, insider threats, and supply chain compromise
- Evaluate consequences for each threat scenario considering safety impacts, production losses, regulatory penalties, and reputational damage
- Select countermeasures achieving required security level targets while respecting operational constraints and safety certifications
- Integrate findings with safety risk assessments to ensure comprehensive coverage of hazards arising from both random failures and malicious attacks
- Document assessment methodology, findings, and risk treatment decisions to demonstrate compliance during audits
| Risk model characteristic | Traditional probability-based | Modern consequence-based |
|---|---|---|
| Primary metric | Likelihood times impact score | Consequence severity and exploitability |
| Threat assumption | Random events and opportunistic attacks | Motivated adversaries with specific objectives |
| Vulnerability prioritization | Highest probability risks first | Greatest consequence risks regardless of likelihood |
| Control effectiveness | Reduces probability of occurrence | Limits consequences when breaches occur |
| Compliance alignment | Audit checklist completion | Demonstrated risk reduction and resilience |
Your risk management strategy guide 2026 must emphasize that compliance requires ongoing risk assessment, not one-time evaluation. Regulatory frameworks expect you to reassess risks when systems change, new threats emerge, or incidents reveal assessment gaps. Establish triggers for reassessment including major system upgrades, organizational changes affecting security responsibilities, newly discovered vulnerabilities in deployed equipment, and lessons learned from industry incidents affecting similar technologies.
Combining safety and cybersecurity risk processes delivers multiple advantages beyond regulatory compliance. Integrated assessment identifies scenarios where cyber attacks could trigger safety hazards, ensuring your countermeasures address both digital vulnerabilities and physical consequences. You avoid duplicating effort by leveraging common risk analysis techniques, asset inventories, and documentation requirements across both domains. Unified risk registers help leadership understand total organizational risk exposure rather than viewing safety and security as separate concerns.
The assessment process generates actionable priorities for security investments by quantifying potential consequences in business terms. When you demonstrate that a compromised batch control system could cause $5 million in product loss, regulatory fines, and remediation costs, leadership can make informed decisions about allocating $200,000 for network segmentation and monitoring tools. Consequence-based evaluation translates technical vulnerabilities into business impacts that justify security spending and drive organizational commitment to risk reduction.
Explore Stonos Solutions' industrial security expertise
Understanding industrial security risk assessment methodologies provides the foundation, but implementing comprehensive protection requires specialized expertise and proven frameworks. Stonos Solutions delivers penetration testing services specifically designed for operational technology environments, where traditional testing approaches could disrupt production or trigger safety systems. Our team holds CISSP, PSP, and industry certifications that demonstrate deep knowledge of both cybersecurity principles and industrial operations.

Our custom development and automation capabilities help organizations implement monitoring solutions for constrained industrial components that cannot support standard security controls. We build physics-based anomaly detection systems, protocol analyzers, and correlation engines that provide visibility into vulnerable assets while respecting safety certifications and operational requirements. These tailored solutions integrate with your existing infrastructure to enhance resilience without requiring equipment replacement.
Comprehensive security services from Stonos Solutions address the full lifecycle of industrial risk management, from initial assessment through countermeasure implementation and ongoing monitoring. We help regulated industries meet compliance mandates while building operational resilience that protects against evolving threats. Our experience across healthcare, manufacturing, and critical infrastructure sectors ensures we understand your specific challenges and regulatory context.
FAQ
Why is assessing industrial security risks essential?
Industrial security risk assessment ensures regulatory compliance while protecting operational technology systems that control physical processes. Unlike IT systems where breaches primarily affect data, compromised industrial controls can cause safety hazards, production losses, and environmental incidents. Regulated industries face specific mandates requiring documented risk evaluation and mitigation.
How does IEC 62443 improve industrial risk assessments?
IEC 62443 provides a structured Zone and Conduit methodology that partitions complex industrial systems into manageable security domains. This framework focuses protection efforts on boundaries and communication paths rather than attempting uniform security across diverse equipment. The standard defines security level targets that align technical controls with operational requirements and risk tolerance.
What special considerations exist for safety-critical sensors?
Sensors in hazardous locations must comply with intrinsic safety standards that limit electrical energy below ignition thresholds. These constraints prevent implementing cryptographic processors, secure boot mechanisms, or other digital security controls requiring computational resources. Alternative approaches use physics-based monitoring and communication analysis to detect manipulation attempts without modifying the sensors themselves.
How can I integrate safety and cybersecurity risk assessments effectively?
Establish joint review processes where safety engineers and cybersecurity professionals evaluate scenarios collaboratively, identifying risks neither discipline would recognize independently. Use common risk analysis techniques and unified documentation to avoid duplication while ensuring comprehensive coverage. Focus on scenarios where cyber attacks could trigger safety hazards, ensuring countermeasures address both digital vulnerabilities and physical consequences simultaneously.
Recommended
- Top 7 security compliance tips for 2026 success - Stonos Solutions Blog
- How to Conduct Security Risk Assessment for HIPAA Compliance - Stonos Solutions Blog
- Risk management strategy guide 2026: advanced tactics - Stonos Solutions Blog
- Security Consulting for Integrators: Enabling Resilience - Stonos Solutions Blog
- Compliance bei Automatisierung – Schutz vor Risiken und Bußgeldern - EcomTask
- 7 passi per una checklist di sicurezza industriale efficace
Louis Romano
Need Security Consulting?
Our expert team is ready to help you enhance your security posture.
Contact Us Today Download Capability StatementRelated Articles
Why Use Vulnerability Analysis—Ensuring Security Compliance
Vulnerability analysis helps organizations prevent breaches, meet regulatory standards, and prioritize risks. Learn benefits, requirements, and key processes.
Read MoreCISSP certification: value, requirements, and career impact
Discover how CISSP certification drives career growth, supports regulatory compliance, and positions IT professionals for leadership roles in regulated industries.
Read MoreWhy follow cybersecurity trends 2026 for compliance
Discover why tracking cybersecurity trends in 2026 is essential for regulatory compliance and risk management across AI, quantum computing, and supply chain threats.
Read More