Regulatory compliance explained: key changes for 2026
Regulatory compliance explained: key changes for 2026

Penalties for regulatory non-compliance are no longer theoretical. NYDFS penalties start at $2,500 per day for organizations that fall short of the updated cybersecurity requirements taking effect this year. Across sectors, compliance officers are navigating a wave of new mandates, amended frameworks, and enforcement postures that demand far more than a policy binder on a shelf. This guide walks you through what regulatory compliance means in 2026, which rules are changing, how enforcement is shifting toward proof over promises, and the practical steps your team can take right now to stay ahead.
Table of Contents
- What is regulatory compliance?
- Key compliance mandates taking effect in 2026
- New enforcement priorities: From policy to proof
- Pitfalls and how to avoid them in 2026 compliance
- Practical steps to prepare for 2026 and beyond
- How Stonos Solutions can accelerate your compliance for 2026
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Evidence is everything | 2026 enforcement shifts require demonstrating real proof of compliance in daily operations. |
| Mandates are stricter | New rules span cyber, AI, third-party risk, and data—penalties are tougher and deadlines tighter. |
| Start early | Early compliance preparation reduces costs and minimizes the risk of facing major penalties. |
| Avoid hidden pitfalls | Overlooked risks such as shadow AI and MFA exceptions can undermine your overall program. |
| Leverage expert support | Partnering with compliance experts can streamline readiness and accelerate results for 2026. |
What is regulatory compliance?
Regulatory compliance means your organization consistently meets the legal, technical, and operational requirements set by governing bodies relevant to your industry. In 2026, that definition carries more weight than ever. Regulators are no longer satisfied with documented intent. They want demonstrated, continuous adherence backed by evidence.
The stakes are real. One-third of regulatory teams missed key requirements last year, with resulting losses ranging from $500,000 to $1 million per incident. That figure should reset how your board thinks about compliance budgets.
The stakeholders affected span every layer of your organization:
- Compliance officers responsible for tracking and reporting obligations
- IT and security leads managing technical controls and monitoring
- Boards and executives accountable for governance and risk posture
- Third-party vendors whose gaps can become your liability
"Organizations that treat compliance as a checkbox exercise are the ones generating the headlines. The cost of a gap is no longer just a fine. It's market position, customer trust, and sometimes the business itself."
For a sharper foundation before diving into specifics, review these security compliance tips that apply across regulated industries. The 2026 regulatory mandates landscape is broad, but understanding the core definition helps you prioritize where to focus first.
Key compliance mandates taking effect in 2026
The regulatory calendar for 2026 is dense. Several major frameworks are either going live or seeing significant amendments, and each carries its own requirements, penalties, and deadlines.
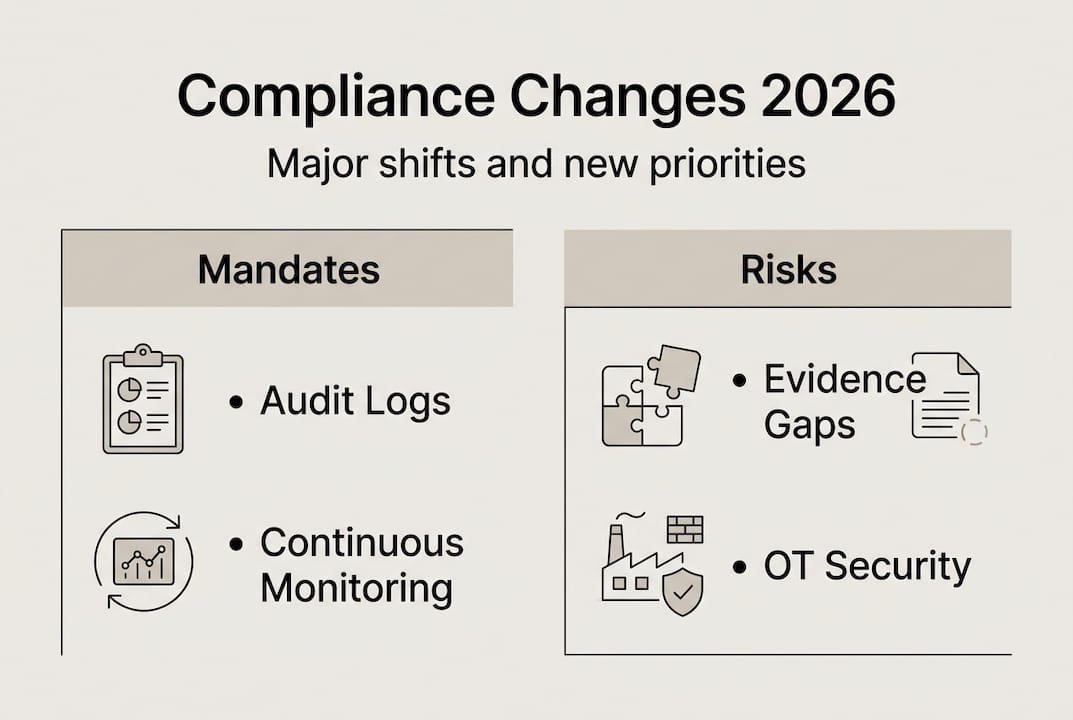
The three changes hitting compliance teams hardest right now are:
- Universal MFA and continuous monitoring under the updated NYDFS Cybersecurity Regulation, with penalties of $2,500 per day for violations
- AI governance documentation under the EU AI Act, where high-risk AI fines reach €35 million or 7% of global turnover
- Third-party ICT risk oversight under DORA, requiring financial entities to audit and document every critical vendor relationship
Here is a snapshot of the major frameworks you need to track:
| Regulator / Framework | Sector | Main requirements | Penalties | Key deadline |
|---|---|---|---|---|
| NYDFS Cybersecurity Reg | Financial services | Universal MFA, continuous monitoring, CISO accountability | $2,500/day | In effect 2026 |
| CIRCIA | Critical infrastructure | Incident reporting within 72 hours, cyber incident disclosure | Civil penalties | Rulemaking 2026 |
| SEC Cybersecurity Rules | Public companies | Material incident disclosure, board oversight | Enforcement actions | Ongoing |
| EU AI Act | All sectors (EU nexus) | Risk classification, technical documentation, human oversight | Up to €35M or 7% turnover | August 2, 2026 |
| DORA | EU financial entities | ICT resilience testing, third-party risk management | Regulator-set fines | In effect |
| FinCEN / BoI Reporting | US businesses | Beneficial ownership disclosure | $500/day, up to $10,000 | Active |
| CCPA Expansions | California businesses | Expanded consumer rights, opt-out requirements | $7,500 per intentional violation | Ongoing |
Stat callout: Real estate transaction reporting violations under the FinCEN Geographic Targeting Orders can reach $286,184 per violation. That number alone justifies a dedicated vendor review.
For organizations in industrial and manufacturing sectors, the convergence of OT security requirements and these new frameworks adds another layer of complexity. Our analysis of security in manufacturing covers how these mandates intersect with operational environments. Pairing that with strong risk management strategies gives your team a workable starting point. The 2026 compliance predictions from industry analysts confirm that enforcement intensity will only increase through the year.
New enforcement priorities: From policy to proof
Here is the single biggest shift compliance officers need to internalize for 2026: regulators are no longer reviewing your policies. They are auditing your evidence.
CIRCIA and SEC enforcement has moved to what analysts call execution-focused compliance. That means audit logs, technical artifacts, timestamped control records, and documented incident responses. A well-written policy with no supporting evidence is a liability, not a defense.
The EU AI Act adds another dimension. It mandates human oversight mechanisms and full technical documentation for high-risk AI systems, while DORA requires ICT resilience testing results to be on file and available for regulator review.
| Compliance element | Old approach | New evidence requirement | Risk if absent |
|---|---|---|---|
| Access controls | Written policy | MFA logs, access review records | Regulatory fine, breach liability |
| Incident response | IR plan document | Drill records, actual response timelines | Enforcement action |
| Vendor risk | Vendor questionnaire | Audit reports, contract controls, monitoring logs | Third-party breach liability |
| AI governance | Internal AI policy | Risk classification docs, human oversight records | EU AI Act fines |
| Cyber monitoring | Periodic scans | Continuous monitoring dashboards, alerts log | NYDFS, CIRCIA penalties |
"Enforcement is moving from guidance to proof. Organizations that cannot produce technical artifacts on demand will face the same consequences as those with no program at all." — Ropes & Gray, 2026 outlook
Pro Tip: Run a readiness audit focused entirely on evidence gaps, not policy gaps. Ask your team: if a regulator walked in tomorrow, what could you hand them? If the answer is a document rather than a log or a report, you have work to do.
The contrast between US and EU approaches is worth noting. US federal regulators are showing some flexibility in enforcement timelines, particularly for smaller entities. The EU is not. The compliance workflow best practices that work in a US-only context may fall short if your organization has any EU market exposure.
For teams building out their evidence architecture, our risk management tactics guide covers control documentation frameworks in detail. If you work with system integrators, the security consulting for integrators resource addresses how evidence requirements flow through the supply chain. The evidence-based compliance resources on our site provide additional frameworks for structuring your documentation program.
Pitfalls and how to avoid them in 2026 compliance
Knowing what the rules require is only half the battle. The organizations generating enforcement headlines in 2026 are not always the ones ignoring compliance. Many have programs in place but are falling into predictable traps.
The most common pitfalls compliance teams are hitting right now include:
- MFA exceptions left open for legacy systems or executive accounts, creating audit vulnerabilities
- Weak asset inventories that leave unmanaged devices and shadow IT outside your control perimeter
- Shadow AI deployments where business units adopt AI tools without governance review or documentation
- Quantum risk avoidance where teams delay post-quantum cryptography planning despite NIST guidance
- Vendor due diligence gaps where third-party risk assessments are completed once and never updated
The 2026 compliance mechanics that regulators are scrutinizing most closely are continuous monitoring, CISO-approved compensating controls, and documented quantum readiness planning. If your program is missing any of these, you are exposed.
Avoiding these pitfalls requires investment in three areas. First, deploy continuous monitoring tools that generate real-time logs rather than periodic snapshots. Second, apply rigorous documentation discipline so every control decision has a paper trail. Third, clarify which compensating controls have explicit CISO approval and document that approval formally.
Pro Tip: Conduct a tabletop exercise specifically designed around 2026 risks. Simulate a shadow AI incident, a vendor breach, or a quantum-related key compromise. The gaps your team cannot answer in the room are the gaps regulators will find in an audit.
A thorough risk assessment process is the foundation for identifying these exposure points before regulators do. For organizations that need to validate technical controls, penetration testing tools can surface vulnerabilities that documentation reviews miss entirely. Pairing those findings with network monitoring insights gives your team a more complete picture of your actual risk surface.
Practical steps to prepare for 2026 and beyond
The organizations that will navigate 2026 with the least friction are the ones that started preparing early. Early compliance preparation can reduce total compliance costs by up to 60%. That is not a marginal efficiency gain. That is a budget-level argument for moving now rather than waiting for an enforcement trigger.
Here is the action plan your team should be executing:
- Inventory and control review. Map every asset, system, and data flow against the specific requirements of each applicable framework. Identify gaps between your current controls and what 2026 mandates require.
- Evidence generation architecture. Build or upgrade your logging, monitoring, and documentation systems so they produce audit-ready artifacts automatically. Manual evidence collection does not scale.
- Vendor and third-party checks. Reassess every critical vendor relationship against DORA, NYDFS, and SEC third-party risk requirements. Require updated audit reports, not just questionnaires.
- Incident reporting drills. Practice your 72-hour CIRCIA reporting workflow and your SEC material incident disclosure process. Regulators will check whether your team can actually execute under pressure.
- AI governance review. Catalog every AI tool in use across the organization, classify each by EU AI Act risk tier, and assign documentation and oversight responsibilities.
Future-proofing your compliance program means building for the next wave, not just the current one. Post-quantum cryptography planning, AI governance maturity, and automated evidence generation are the three areas where investment today will pay off across multiple regulatory cycles. The 2026 compliance guide from ComplianceHub provides additional context on where enforcement is heading beyond this year's deadlines. For a practical checklist to keep your program on track, the compliance tips for 2026 resource covers the operational details.
How Stonos Solutions can accelerate your compliance for 2026
The gap between knowing what compliance requires and actually demonstrating it to regulators is where most organizations struggle. Stonos Solutions works with compliance officers and security teams across healthcare, government, manufacturing, and enterprise sectors to close that gap with precision.

Our penetration testing services are structured to validate the technical controls that DORA, NYDFS, and CIRCIA now require as evidence, not just as policy. We generate the audit-ready artifacts your team needs to satisfy regulator requests on demand. For organizations managing EU AI Act documentation or SEC disclosure workflows, our custom automation solutions streamline evidence generation and reduce the manual burden on your compliance staff. If you are ready to move from policy to proof, our team is ready to help you build the program that gets you there.
Frequently asked questions
What is the penalty for NYDFS cybersecurity non-compliance in 2026?
Organizations face penalties starting at $2,500 per day for violations under the updated NYDFS Cybersecurity Regulation, with amounts scaling based on the severity and duration of the gap.
What are the key deadlines for the EU AI Act in 2026?
High-risk AI system requirements must be fully in place by August 2, 2026, with fines reaching €35 million or 7% of global annual turnover for non-compliance.
How can early compliance preparation benefit my organization in 2026?
Early preparation reduces total compliance costs by up to 60% and significantly lowers the probability of enforcement actions by giving your team time to close gaps before regulators identify them.
What main shift should compliance teams expect in 2026 enforcement?
Regulators are moving from reviewing static policy documents to demanding continuous, real-time evidence of control effectiveness, including audit logs, monitoring records, and documented incident responses.
What is the largest compliance risk around AI and data in 2026?
Gaps in AI governance documentation and human oversight mechanisms are the highest-risk exposure points under the EU AI Act and SEC rules, with fines that can reach into the tens of millions for high-risk system failures.
Recommended
- Top 7 security compliance tips for 2026 success - Stonos Solutions Blog
- Risk management strategy guide 2026: advanced tactics - Stonos Solutions Blog
- Top risk management strategies for IT security 2026 - Stonos Solutions Blog
- Security Consulting for Integrators: Enabling Resilience - Stonos Solutions Blog
- Korp.ph | Regulatory trends in the Philippines 2026: What businesses must know
- Gold trading regulations 2026: 75% AML penalties highlight risks
Louis Romano
Need Security Consulting?
Our expert team is ready to help you enhance your security posture.
Contact Us Today Download Capability StatementRelated Articles
Why regulatory compliance matters: reduce risk, protect your org
Learn why regulatory compliance matters for healthcare, government, and industrial sectors. Discover frameworks and strategies to reduce risk and protect your organization.
Read MoreWhy Use Vulnerability Analysis—Ensuring Security Compliance
Vulnerability analysis helps organizations prevent breaches, meet regulatory standards, and prioritize risks. Learn benefits, requirements, and key processes.
Read MoreRegulatory Compliance Explained: Build Stronger Security
Learn what regulatory compliance really means, how the management cycle works, and how to navigate conflicts to build stronger security and organizational trust.
Read More